Cisco WS-C2980G-A Software Guide - Page 449
Understanding How Kerberos Authentication Works
 |
UPC - 746320423555
View all Cisco WS-C2980G-A manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 449 highlights
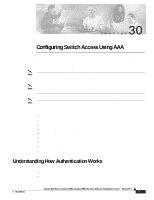
Chapter 30 Configuring Switch Access Using AAA Understanding How Authentication Works RADIUS authentication is disabled by default. You can enable RADIUS authentication and other authentication methods at the same time. You can specify which method to use first using the primary keyword. If local authentication is disabled and you then disable all other authentication methods, local authentication is reenabled automatically. Understanding How Kerberos Authentication Works Kerberos is a client-server-based secret-key network authentication method that uses a trusted Kerberos server to verify secure access to both services and users. In Kerberos, this trusted server is called the key distribution center (KDC). The KDC issues tickets to validate users and services. A ticket is a temporary set of electronic credentials that verify the identity of a client for a particular service. These tickets have a limited life span and can be used in place of the standard user password authentication mechanism if a service trusts the Kerberos server from which the ticket was issued. If the standard user password method is used, Kerberos encrypts user passwords into the tickets, ensuring that passwords are not sent on the network in clear text. When you use Kerberos, passwords are not stored on any machine (except for the Kerberos server) for more than a few seconds. Kerberos also guards against intruders who might pick up the encrypted tickets from the network. Table 30-1 defines terms used in Kerberos. Table 30-1 Kerberos Terminology Term Kerberized Kerberos credential Kerberos identity Kerberos principal Kerberos realm Kerberos server Key distribution center (KDC) Service credential Definition Applications and services that have been modified to support the Kerberos credential infrastructure. General term referring to authentication tickets, such as ticket granting tickets and service credentials. Kerberos Credentials verify the ticket of a user or service. If a network service decides to trust the Kerberos server that issued the ticket, it can be used in place of retyping in a username and password. Credentials have a default life span of 8 hours. (See Kerberos principal.) Who you are or what a service is according to the Kerberos server. Also known as a Kerberos identity. A domain consisting of users, hosts, and network services that are registered to a Kerberos server. (The Kerberos server is trusted to verify the identity of a user or network service to another user or network service.) Kerberos realms must always be in uppercase characters. A daemon running on a network host. Users and network services register their identity with the Kerberos server. Network services query the Kerberos server to authenticate other network services. A Kerberos server and database program running on a network host that allocates the Kerberos credentials to different users or network services. A credential for a network service. When issued from the KDC, this credential is encrypted with the password that is shared by the network service and the KDC and with the user's TGT. 78-15486-01 Catalyst 4500 Series, Catalyst 2948G, Catalyst 2980G Switches Software Configuration Guide-Release 8.1 30-5