3Com 2928 User Guide - Page 361
Then, it encrypts the password information using a randomly generated challenge
 |
UPC - 662705557113
View all 3Com 2928 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 361 highlights
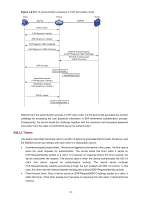
Figure 1-8 802.1X authentication procedure in EAP relay mode Client EAPOL Device EAPOR Server EAPOL-Start EAP-Request / Identity EAP-Response / Identity EAP-Request / MD5 challenge RADIUS Access-Request (EAP-Response / Identity) RADIUS Access-Challenge (EAP-Request / MD5 challenge) EAP-Response / MD5 challenge EAP-Success RADIUS Access-Request (EAP-Response / MD5 challenge) RADIUS Access-Accept (EAP-Success) Port authorized Handshake request ( EAP-Request / Identity ) Handshake response ( EAP-Response / Identity ) Handshake timer ...... EAPOL-Logoff Port unauthorized 1) When a user launches the 802.1X client software and enters the registered username and password, the 802.1X client software generates an EAPOL-Start frame and sends it to the device to initiate an authentication process. 2) Upon receiving the EAPOL-Start frame, the device responds with an EAP-Request/Identity packet for the username of the client. 3) When the client receives the EAP-Request/Identity packet, it encapsulates the username in an EAP-Response/Identity packet and sends the packet to the device. 4) Upon receiving the EAP-Response/Identity packet, the device relays the packet in a RADIUS Access-Request packet to the authentication server. 5) When receiving the RADIUS Access-Request packet, the RADIUS server compares the identify information against its user information table to obtain the corresponding password information. Then, it encrypts the password information using a randomly generated challenge, and sends the challenge information through a RADIUS Access-Challenge packet to the device. 6) After receiving the RADIUS Access-Challenge packet, the device relays the contained EAP-Request/MD5 Challenge packet to the client. 7) When receiving the EAP-Request/MD5 Challenge packet, the client uses the offered challenge to encrypt the password part (this process is not reversible), creates an EAP-Response/MD5 Challenge packet, and then sends the packet to the device. 8) After receiving the EAP-Response/MD5 Challenge packet, the device relays the packet through a RADIUS Access-Request packet to the authentication server. 1-6