3Com 2928 User Guide - Page 385
AAA Configuration, Overview, Introduction to AAA
 |
UPC - 662705557113
View all 3Com 2928 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 385 highlights
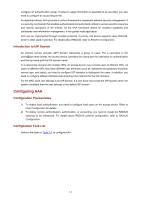
1 AAA Configuration Overview Introduction to AAA Authentication, Authorization, and Accounting (AAA) provides a uniform framework for configuring these three security functions to implement network security management. AAA usually uses a client/server model, where the client runs on the network access server (NAS) and the server maintains user information centrally. In an AAA network, a NAS is a server for users but a client for the AAA servers, as shown in Figure 1-1. Figure 1-1 AAA networking diagram When a user tries to establish a connection to the NAS and to obtain the rights to access other networks or some network resources, the NAS authenticates the user or the corresponding connection. The NAS takes the responsibility to transparently pass the user's AAA information to the server (RADIUS server, for example). The RADIUS protocol defines how a NAS and a server exchange user information between them. In the AAA network shown in Figure 1-1, there are two RADIUS servers. You can determine which of the authentication, authorization and accounting functions should be assumed by which servers. For example, you can use RADIUS server 1 for authentication and authorization, and RADIUS server 2 for accounting. The three security functions are described as follows: z Authentication: Identifies remote users and judges whether a user is legal. z Authorization: Grants different users different rights. For example, a user logging into the server can be granted the permission to access and print the files in the server. z Accounting: Records all network service usage information of users, including the service type, start and end time, and traffic. In this way, accounting can be used for not only charging, but also network security surveillance. You can use AAA to provide only one or two security functions, if desired. For example, if your company only wants employees to be authenticated before they access specific resources, you only need to 1-1