HP t420 Administrator Guide 8 - Page 172
security
 |
View all HP t420 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 172 highlights
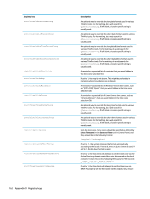
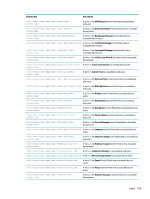
Registry key root/screensaver/off root/screensaver/origImageCopyPath root/screensaver/solidColor root/screensaver/standby root/screensaver/suspend root/screensaver/timeoutScreensaver root/screensaver/timeoutSleep root/screensaver/useSolidColor security Registry key root/security/SecurityFeaturs/ SpeculativeStoreBypassControl root/security/authenticationFailDelay root/security/domainEntryMode root/security/enableLockOverride root/security/enableSecretPeek root/security/encryption/identity/ encryptedSecretCipher root/security/encryption/identity/ encryptedSecretTTL root/security/encryption/identity/ encryptedSecretTTLnonSSO 160 Appendix D Registry keys Description Sets the timeout delay in minutes before the monitor turns off. This is the path where the custom image is saved when mode is set to Default. If useSolidColor is on and enableCustomLogo is off, this solid color is used for the screen saver. Sets the timeout delay in minutes before the monitor goes into standby mode. Sets the timeout delay in minutes before the monitor goes into suspend mode. Sets the timeout delay in minutes before the screen saver starts. Sets the timeout delay in minutes before the thin client goes into the Sleep state. If set to 1 and enableCustomLogo is off, the value of the solidColor key is used by the screen saver. Description Controls whether mitigations for Speculative Store Bypass (CVE-2018-3639) are enabled. By default, these mitigations are not enabled. To enable them, set the key value to on. For any change to this key to take effect, reboot the computer. Sets the approximate time, in milliseconds, to delay after a failed login attempt. The actual time will vary plus or minus 25% of this value. For example, use a value of 3000 to obtain a delay of approximately 3 seconds. If set to 1, the domain is expected to be entered in a separate text field labeled Domain. if set to 0, the domain is expected to be entered as part of the User field. If set to 1, administrators can override the screen lock of a local desktop. If set to 1, password and PIN dialogs will have a button that, while selected, will show the entered password/PIN in clear text. Sets the algorithm for symmetric encryption of a secret. All algorithms use an appropriate amount of random salt, which is regenerated each time the secret is stored. The encryption key is different on each thin client, and encryption and decryption are available only to authorized programs. The supported cipher list includes most OpenSSL ciphers and ChaCha20-Poly1305. Sets the number of seconds since the last successful login that a stored encrypted secret will be considered valid. If set to a negative number, encrypted secrets will not time out. Specifies the number of seconds that a stored, non-SSO encrypted secret is considered valid. If set to a nonpositive number, encrypted secrets do not time out.