IBM 26K6477 User Guide - Page 5
Contents - jobs
 |
View all IBM 26K6477 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 5 highlights
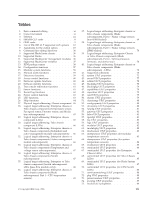
Contents Figures v Tables vii Preface ix About this guide xi Accessibility xi Accessibility features for the SMASH Proxy . . . xi Who should read this guide . . . . . xiii Chapter 1. Introduction 1 Chapter 2. SMASH: An overview . . . . 3 SMASH CLP architecture overview 3 SMASH CLP architectural model 3 Addressing managed elements 4 Chapter 3. Using the SMASH CLP command line 7 SMASH CLP syntax 7 SMASH CLP verbs and OEM verb extensions . . . 7 SMASH CLP supported verbs and descriptions . . 8 SMASH CLP verb options 9 SMASH CLP supported verb options and descriptions 9 SMASH CLP supported targets 17 Physical and logical target addressing . . . . 18 Addressing associations 18 SMASH CLP profiles 29 SMASH CLP supported command target properties 29 Command line editing 29 Command history 30 Command authority 30 Chapter 4. The SMASH Proxy: An overview 31 The SMASH Proxy architectural model . . . . . 32 Chapter 5. Using the SMASH Proxy . . 35 Before you begin 35 SMASH Proxy supported BladeCenter components 36 Installing the SMASH Proxy 37 Configuring SNMPv3 in the SMASH Proxy. . . . 39 SNMPv3 configuration in the MM 40 SLP configuration in the MM 44 Configuring the credentials server 45 Accessing the SMASH Proxy: Remote user access . 45 SSH access 46 Telnet access 47 Accessing the SMASH Proxy: Local user access . . 47 Uninstalling the SMASH Proxy 48 Chapter 6. Using SMASH Proxy functionality 49 OEM verbs 49 SMASH Proxy functions 57 SMASH Proxy nonaddressing associations and supported physical and logical targets . . . . . 64 Handling general UFcTs compared to specific UFcTs 71 SMASH Proxy supported targets (by UFcT) and associated command target properties . . . . . 72 SMASH Proxy command target property descriptions 94 CIM property types 102 Managing multiple chassis 103 Handling chassis credentials 103 Administering text console redirection . . . . . 105 Reviewing job status 106 Using pass-thru modules 107 Implementing redundant MMs 107 Turning on debug for the SMASH Proxy . . . . 107 Chapter 7. SMASH-related documentation 109 Chapter 8. Printable PDF 111 Appendix. Notices 113 Trademarks 115 Glossary 117 Terms 117 Index 121 © Copyright IBM Corp. 2006 iii