Konica Minolta C250i bizhub C360i/C300i/C250i Security Operations User Manual - Page 13
Enhanced security mode, Precautions for operation control
 |
View all Konica Minolta C250i manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 13 highlights
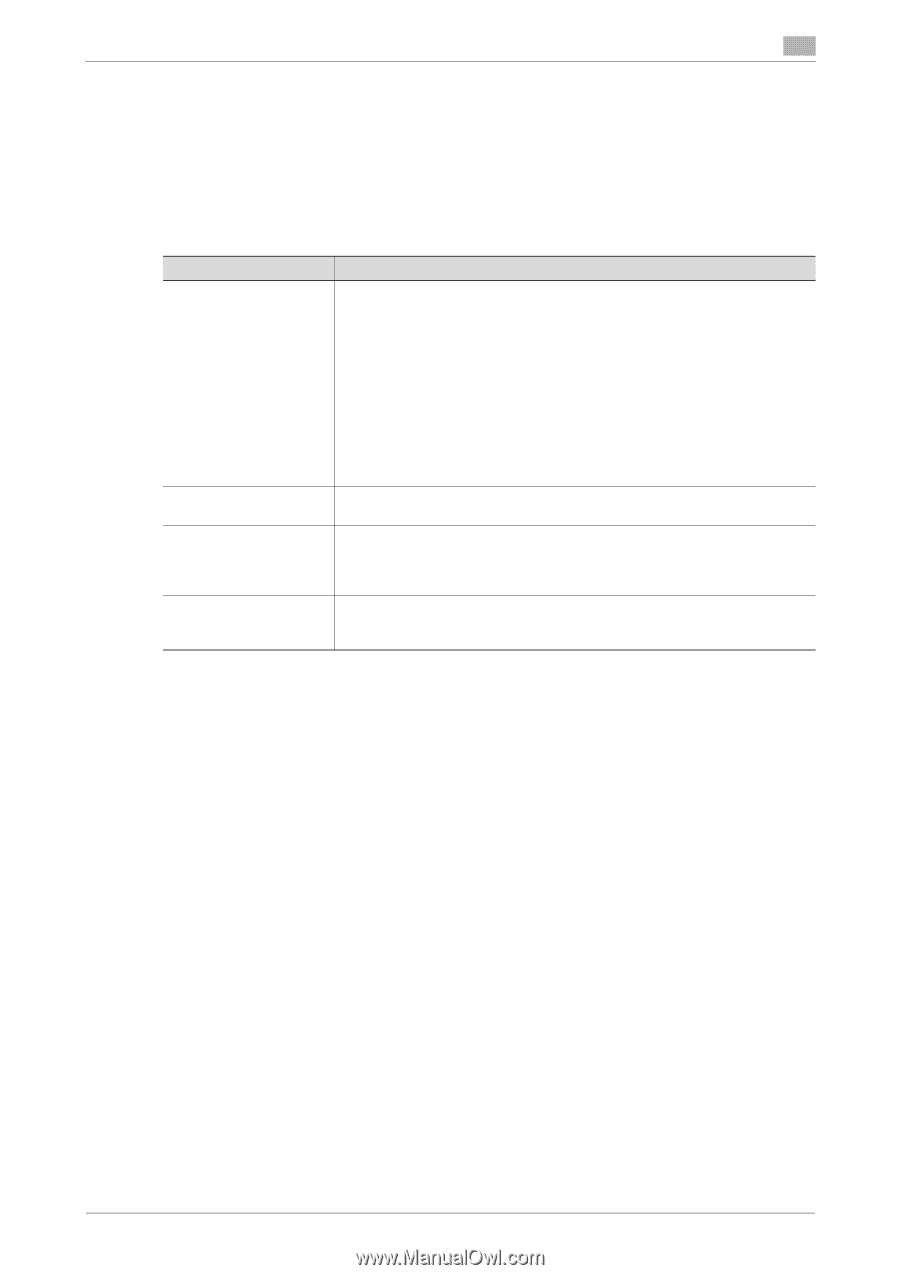
1.3 Enhanced security mode 1 1.3 Enhanced security mode Setting the [Enhanced Security Mode] to [ON] will validate the security function of this machine. For details of the settings of different security functions to be changed by turning [ON] the [Enhanced Security Mode], see page 2-10. 1.3.1 Major security functions in operation under ISO15408 certification The following describes major security functions in operation under ISO15408 certification. Function Identification and authentication function User limiting function Auditing function Network communication protecting function Description Access control is then provided through password authentication for any access to the Administrator Mode, user authentication mode, User Box, and a User Box data file. Access is thereby granted only to the authenticated user. A password that can be set must meet the Password Rules. The machine does not accept setting of an easily decipherable password. For details of the Password Rules, see page 1-14. If a wrong password is entered, during password authentication, a predetermined number of times (once to three times.) or more set by the administrator, the machine determines that it is unauthorized access through Prohibited Functions, prohibiting any further entry of the password. By prohibiting the password entry operation, the machine prevents unauthorized use or removal of data. The administrator is responsible for resetting the prohibition of the password entry operation. For details, see page 2-19. Specific functions to be used by each user may be limited. For details, see page 2-24. Information including operations performed on the machine and a job history can be stored in the Storage or log server. Setting the job log (audit log) allows an illegal act or inadequate operation performed on the machine to be traced. For details, see page 2-31. Communication data between the machine, client PC, and servers can be encrypted using the IPsec, which prevents information leakage through eavesdropping over the network. For details, see page 2-15. 1.4 Precautions for operation control This machine and the data handled by this machine should be used in an office environment that meets the following conditions. The machine must be controlled for its operation under the following conditions to protect the data that should be protected. 1.4.1 Roles of the owner of the machine The owner (an individual or an organization) of the machine should take full responsibility for controlling the machine, thereby ensuring that no improper operations are performed. - The owner of the machine should have the administrator recognize the organizational security policy and procedure, educate him or her to comply with the guidance and documents prepared by the manufacturer, and allow time for him or her to acquire required ability. The owner of the machine should also operate and manage the machine so that the administrator can configure and operate the machine appropriately according to the policy and procedure. - The owner of the machine should have users of the machine recognize the organizational security policy and procedure, educate them to follow the policy and procedure, and operate and manage the machine so that the users acquire the required ability. - The owner of the machine should vest the user with authority to use the machine according to the organizational security policy and procedure. - The owner of the machine should operate and manage the machine so that the administrator checks the job log (audit log) data at appropriate timing to thereby determine whether a security compromise or a faulty condition has occurred during an operating period. - The owner of the machine must permit only the administrator to handle the job log (audit log) data that has automatically been distributed. The owner of the machine should also operate and manage the machine such that the job log (audit log) data is not illegally accessed, deleted, or altered. bizhub C360i/C300i/C250i/C036DNi/C030DNi/C025DNi 1-9