TP-Link T2500-28TCTL-SL5428E T2500-28TCUN V1 User Guide - Page 238
Port Config, Retry Times, Supplicant Timeout, Port Select, Select, Status, Guest VLAN
 |
View all TP-Link T2500-28TCTL-SL5428E manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 238 highlights
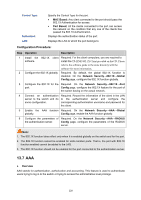
Retry Times: Supplicant Timeout: supplicant during the Quiet Period. Specify the maximum transfer times of the repeated authentication request. Specify the maximum time for the switch to wait for the response from supplicant before resending a request to the supplicant. 13.6.2 Port Config On this page, you can configure the 802.1X features for the ports basing on the actual network. Choose the menu Network Security→802.1X→Port Config to load the following page. Figure 13-24 Port Config The following entries are displayed on this screen: Port Config Port Select: Select: Port: Status: Guest VLAN: Control Mode: Click the Select button to quick-select the corresponding port based on the port number you entered. Select your desired port for configuration. It is multi-optional. Displays the port number. Enable/Disable the 802.1X authentication feature for the port. Enable/Disable the Guest VLAN feature for the port. Specify the Control Mode for the port. • Auto: In this mode, the port will normally work only after passing the 802.1X Authentication. • Force-Authorized: In this mode, the port can work normally without passing the 802.1X Authentication. • Force-Unauthorized: In this mode, the port is forbidden working for its fixed unauthorized status. 228