TP-Link T2500-28TCTL-SL5428E T2500-28TCUN V1 User Guide - Page 43
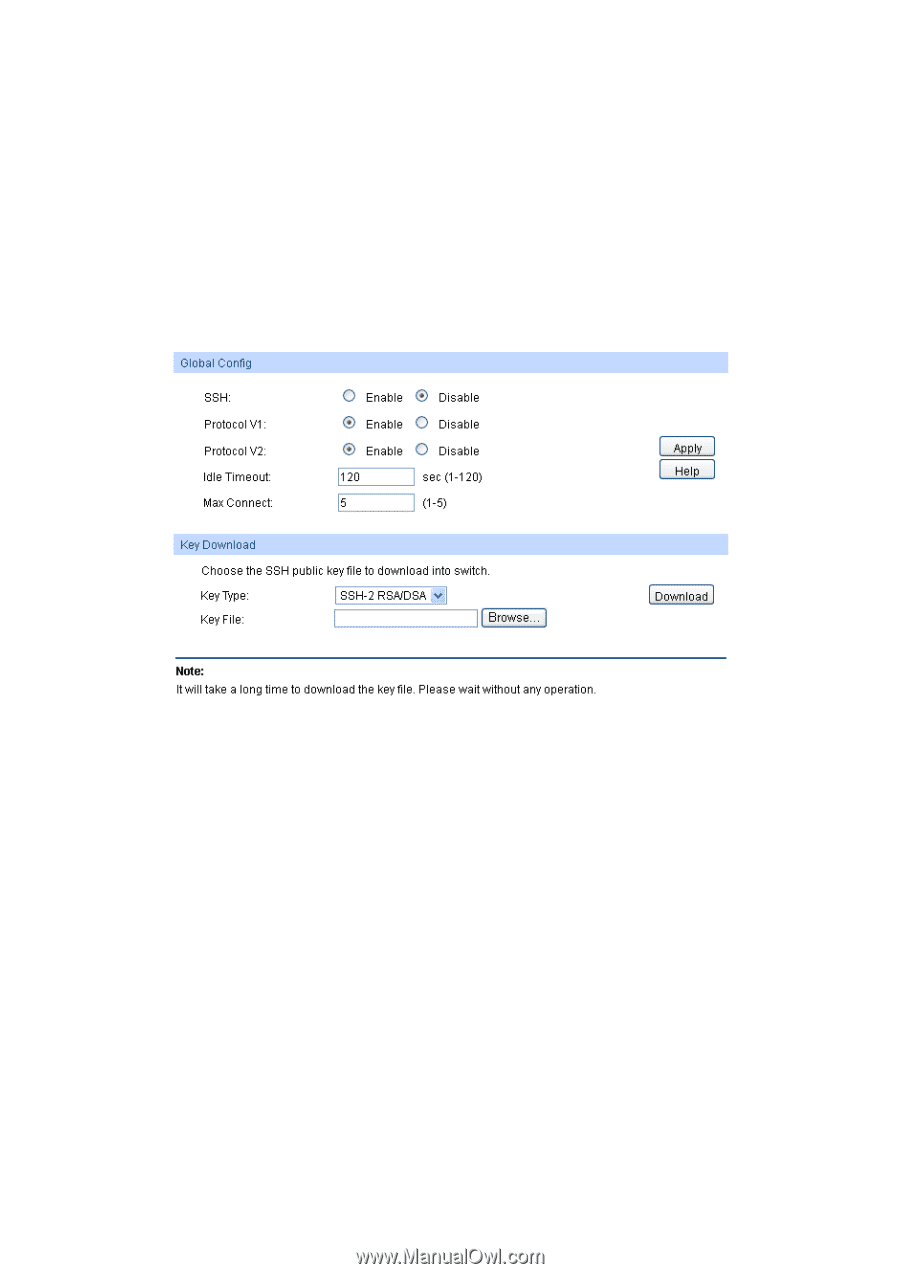
System, Access Security, SSH Config, Global Config, Key Download, Protocol V1, Idle Timeout
 |
View all TP-Link T2500-28TCTL-SL5428E manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 43 highlights
an insecure network environment. It can encrypt all the transmission data and prevent the information in a remote management being leaked. Comprising server and client, SSH has two versions, V1 and V2 which are not compatible with each other. In the communication, SSH server and client can auto-negotiate the SSH version and the encryption algorithm. After getting a successful negotiation, the client sends authentication request to the server for login, and then the two can communicate with each other after successful authentication. This switch supports SSH server and you can log on to the switch via SSH connection using SSH client software. SSH key can be downloaded into the switch. If the key is successfully downloaded, the certificate authentication will be preferred for SSH access to the switch. Choose the menu System→Access Security→SSH Config to load the following page. Figure 4-20 SSH Config The following entries are displayed on this screen: Global Config SSH: Enable/Disable SSH function. Protocol V1: Enable/Disable SSH V1 to be the supported protocol. Protocol V2: Enable/Disable SSH V2 to be the supported protocol. Idle Timeout: Specify the idle timeout time. The system will automatically release the connection when the time is up. The default time is 120 seconds. Max Connect: Specify the maximum number of the connections to the SSH server. No new connection will be established when the number of the connections reaches the maximum number you set. The default value is 5. Key Download Key Type: Select the type of SSH Key to download. The switch supports three types: SSH-1 RSA, SSH-2 RSA and SSH-2 DSA. 33