ZyXEL GS2200-8 User Guide - Page 194
IP Source Guard
 |
View all ZyXEL GS2200-8 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 194 highlights
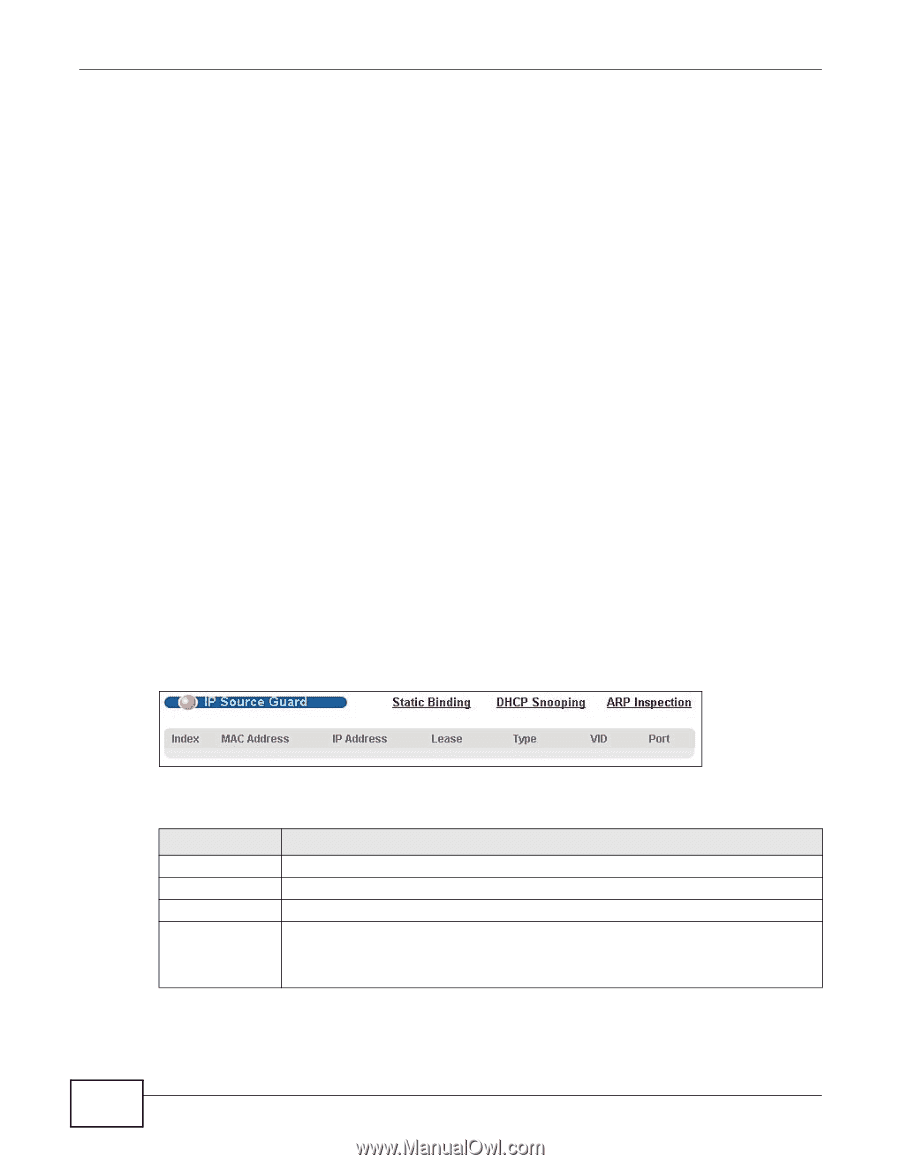
Chapter 25 IP Source Guard • Use the ARP Inspection Port Configure screen (Section 25.9.1 on page 208) to specify whether ports are trusted or untrusted ports for ARP inspection. • Use the ARP Inspection VLAN Configure screen (Section 25.9.2 on page 210) to enable ARP inspection on each VLAN and to specify when the Switch generates log messages for receiving ARP packets from each VLAN. 25.1.2 What You Need to Know The Switch builds the binding table by snooping DHCP packets (dynamic bindings) and from information provided manually by administrators (static bindings). IP source guard consists of the following features: • Static bindings. Use this to create static bindings in the binding table. • DHCP snooping. Use this to filter unauthorized DHCP packets on the network and to build the binding table dynamically. • ARP inspection. Use this to filter unauthorized ARP packets on the network. If you want to use dynamic bindings to filter unauthorized ARP packets (typical implementation), you have to enable DHCP snooping before you enable ARP inspection. 25.2 IP Source Guard Use this screen to look at the current bindings for DHCP snooping and ARP inspection. Bindings are used by DHCP snooping and ARP inspection to distinguish between authorized and unauthorized packets in the network. The Switch learns the bindings by snooping DHCP packets (dynamic bindings) and from information provided manually by administrators (static bindings). To open this screen, click Advanced Application > IP Source Guard. Figure 120 IP Source Guard The following table describes the labels in this screen. Table 67 IP Source Guard LABEL DESCRIPTION Index This field displays a sequential number for each binding. MAC Address This field displays the source MAC address in the binding. IP Address This field displays the IP address assigned to the MAC address in the binding. Lease This field displays how many days, hours, minutes, and seconds the binding is valid; for example, 2d3h4m5s means the binding is still valid for 2 days, 3 hours, 4 minutes, and 5 seconds. This field displays infinity if the binding is always valid (for example, a static binding). 194 GS2200-8/24 User's Guide