Kyocera ECOSYS FS-1135MFP FS-1135MFP Fax Operation Guide - Page 137
Encryption, IMPORTANT, Description of settings at sending and receiving systems, Settings, Sending
 |
View all Kyocera ECOSYS FS-1135MFP manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 137 highlights
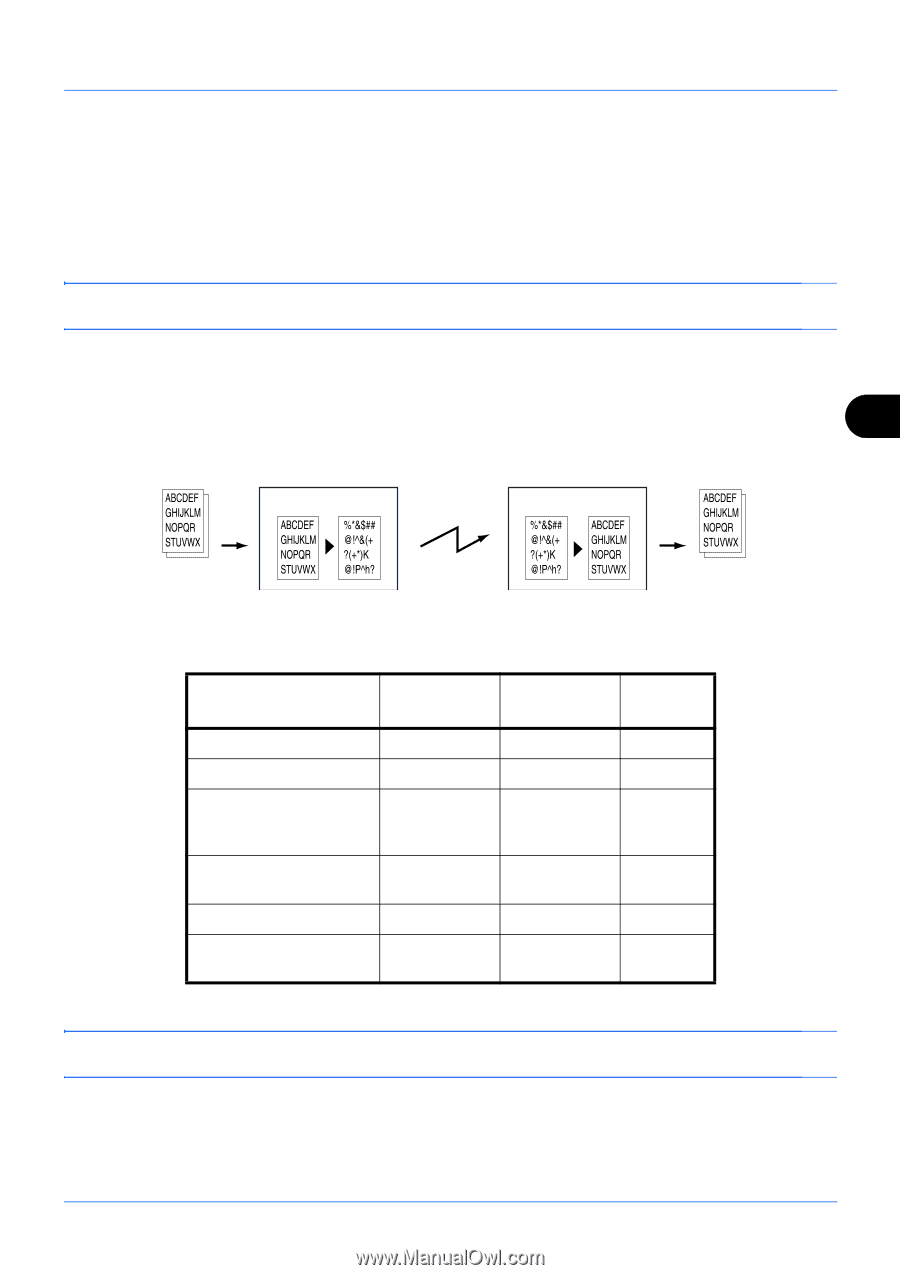
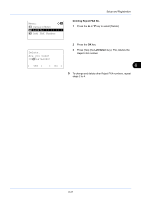
Setup and Registration Encryption This method allows you to communicate with originals encrypted by the sending system. Therefore, even when a third party tries to view the originals in the middle of communication by some means, the third party is prevented from knowing the actual contents of the originals. The originals received are reverted to the originals as they were before transmission (decrypted) by the receiving system, and printed. This is an extremely effective communication method for sending confidential documents that are not to be opened by a third party. IMPORTANT: In order to use encryption communication, the fax of the other party needs to be an our-brand system with the same type of encryption functions. In encryption communication, in order to encrypt and decrypt originals, the sending and receiving systems must use the same 16-digit encryption key. When the encryption key differs between the sending system and the receiving system, the encryption cannot be conducted. Therefore, the sending system and the receiving system need to have the same encryption key and 2-digit key No. registered in advance. 6 Sending system Encrypt Receiving system Decrypt Scan originals Encryption Description of settings at sending and receiving systems Output originals Settings Sending system Receiving system Reference page Encryption Key No. Encryption Key Key No. of Address Book (or when the number is directly dialed) Receiving system encryption box number † Encryption Box No. † Key No. in reception setting (A) 2 digits (C) 16 digits (A) 2 digits (D) 4 digits (B) 2 digits (C) 16 digits (D) 4 digits (B) 2 digits 6-26 6-26 6-26 6-28 6-29 †. When the machine receives originals, the Encryption Box is not used. NOTE: Set the same characters for the numbers indicated by the same letter in parentheses. For example, the same characters should be used as the encryption key (C) in both the sending and receiving systems. 6-25