Netgear M5300-28G3 Web Management User Guide - Page 406
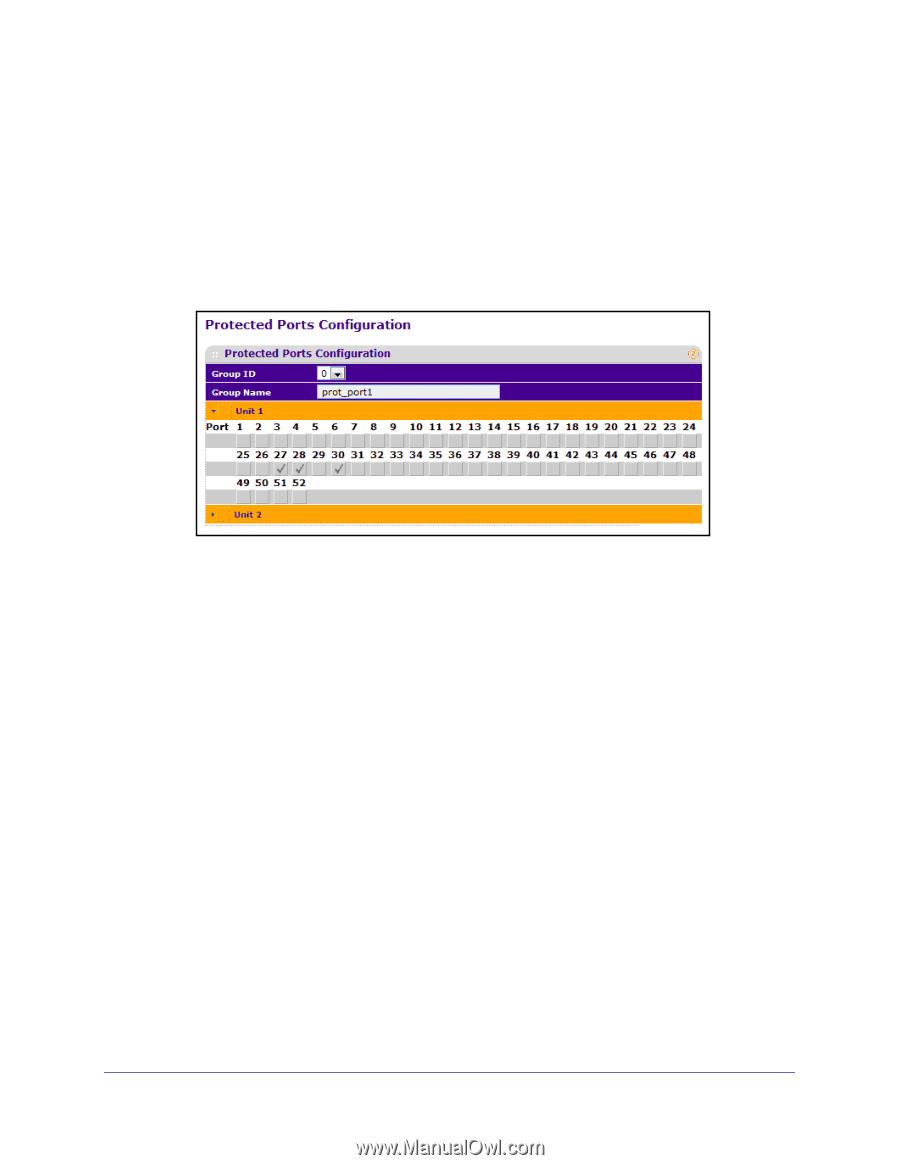
Protected Ports Configuration, Security, Traffic Control, Protected Ports., Group ID, Group Name
 |
View all Netgear M5300-28G3 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 406 highlights
ProSafe M5300 Switch Protected Ports Configuration If a port is configured as protected, it does not forward traffic to any other protected port on the switch, but it will forward traffic to unprotected ports. Use the Protected Ports Configuration page to configure the ports as protected or unprotected. You need read-write access privileges to modify the configuration. To display the Protected Ports Configuration page, click the Security Traffic Control Protected Ports. To configure protected ports: 1. Use Group ID to identify a group of protected ports that can be combined into a logical group. Traffic can flow between protected ports belonging to different groups, but not within the same group. The selection box lists all the possible protected port Group IDs supported for the current platform. The valid range of the Group ID is 0 to 2. 2. Use the optional Group Name field to associate a name with the protected ports group (used for identification purposes). It can be up to 32 alphanumeric characters long, including blanks. The default is blank. This field is optional. 3. Click the orange bar to display the available ports. 4. Click the box below each port to configure as a protected port. The selection list consists of physical ports, protected as well as unprotected. The protected ports are tick-marked to differentiate between them. No traffic forwarding is possible between two protected ports. If left unconfigured, the default state is unprotected. No traffic forwarding is possible between two protected ports. 5. Click REFRESH to refresh the page with the most current data from the switch. 6. Click CANCEL to cancel the configuration on the screen and reset the data on the screen to the latest value of the switch. 7. If you make changes to the page, click APPLY to apply the changes to the system. Configuration changes take effect immediately. Managing Device Security 406