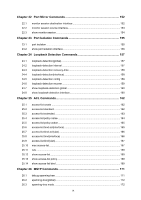
8.6
show etherchannel load-balance
.............................................................................
45
8.7
show lacp
................................................................................................................
46
8.8
show lacp sys-id
......................................................................................................
46
Chapter 9
User Management Commands
.........................................................
48
9.1
user name (password)
............................................................................................
48
9.2
user name (secret)
..................................................................................................
49
9.3
user access-control ip-based
..................................................................................
50
9.4
user access-control mac-based
..............................................................................
51
9.5
user access-control port-based
...............................................................................
51
9.6
telnet
.......................................................................................................................
52
9.7
show user account-list
.............................................................................................
53
9.8
show user configuration
..........................................................................................
53
9.9
show telnet-status
...................................................................................................
53
Chapter 10
HTTP and HTTPS Commands
...........................................................
55
10.1
ip http server
...........................................................................................................
55
10.2
ip http max-users
.....................................................................................................
55
10.3
ip http session timeout
............................................................................................
56
10.4
ip http secure-server
...............................................................................................
57
10.5
ip http secure-protocol
.............................................................................................
57
10.6
ip http secure-ciphersuite
........................................................................................
58
10.7
ip http secure-max-users
.........................................................................................
58
10.8
ip http secure-session
.............................................................................................
59
10.9
ip http secure-server download certificate
...............................................................
59
10.10
ip http secure-server download key
.........................................................................
60
10.11
show ip http configuration
.......................................................................................
61
10.12
show ip http secure-server
......................................................................................
61
Chapter 11
Binding Table Commands
.................................................................
63
11.1
ip source binding
.....................................................................................................
63
11.2
ip dhcp snooping
.....................................................................................................
64
11.3
ip dhcp snooping vlan
.............................................................................................
64
11.4
ip dhcp snooping information option
........................................................................
65
11.5
ip dhcp snooping information strategy
.....................................................................
65
11.6
ip dhcp snooping information remote-id
..................................................................
66
11.7
ip dhcp snooping information circuit-id
....................................................................
67
11.8
ip dhcp snooping trust
.............................................................................................
67
11.9
ip dhcp snooping mac-verify
....................................................................................
68
IV