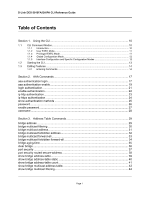
D-Link DES-3010FA/GA/PA CLI Reference Guide
Page 1
Table of Contents
Section 1.
Using the CLI
.....................................................................................................
10
1.1
CLI Command Modes
.............................................................................................................
10
1.1.1
Introduction
...............................................................................................................................
10
1.1.2
User EXEC Mode
.....................................................................................................................
11
1.1.3
Privileged EXEC Mode
.............................................................................................................
11
1.1.4
Global Configuration Mode
.......................................................................................................
12
1.1.5
Interface Configuration and Specific Configuration Modes
......................................................
12
1.2
Starting the CLI
.......................................................................................................................
13
1.3
Editing Features
.....................................................................................................................
14
1.3.1
Entering Commands
.................................................................................................................
14
Section 2.
AAA Commands
................................................................................................
17
aaa authentication login
........................................................................................................
17
aaa authentication enable
.....................................................................................................
19
login authentication
...............................................................................................................
21
enable authentication
............................................................................................................
22
ip http authentication
.............................................................................................................
23
ip https authentication
...........................................................................................................
24
show authentication methods
...............................................................................................
25
password
...............................................................................................................................
26
enable password
...................................................................................................................
27
username
..............................................................................................................................
28
Section 3.
Address Table Commands
................................................................................
29
bridge address
......................................................................................................................
29
bridge multicast filtering
........................................................................................................
30
bridge multicast address
.......................................................................................................
31
bridge multicast forbidden address
.......................................................................................
32
bridge multicast forward-all
...................................................................................................
33
bridge multicast forbidden forward-all
...................................................................................
34
bridge aging-time
..................................................................................................................
35
clear bridge
...........................................................................................................................
36
port security
..........................................................................................................................
37
port security routed secure-address
.....................................................................................
38
show bridge address-table
....................................................................................................
39
show bridge address-table static
..........................................................................................
40
show bridge address-table count
..........................................................................................
41
show bridge multicast address-table
.....................................................................................
42
show bridge multicast filtering
...............................................................................................
44