HP Brocade 8/12c Fabric OS Encryption Administrator's Guide - Page 198
Single fabric deployment - DEK cluster,
 |
View all HP Brocade 8/12c manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 198 highlights
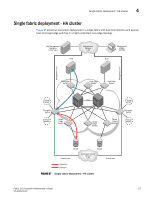
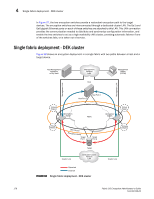
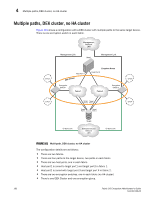
4 Single fabric deployment - DEK cluster In Figure 97, the two encryption switches provide a redundant encryption path to the target devices. The encryption switches are interconnected through a dedicated cluster LAN. The Ge1 and Ge0 gigabit Ethernet ports on each of these switches are attached to this LAN. This LAN connection provides the communication needed to distribute and synchronize configuration information, and enable the two switches to act as a high availability (HA) cluster, providing automatic failover if one of the switches fails, or is taken out of service. Single fabric deployment - DEK cluster Figure 98 shows an encryption deployment in a single fabric with two paths between a host and a target.device. . Key Management Appliance or Key Vault Management Network LAN Management Station (DCFM) Host Management Link Management Link Virtual Target Host Port 1 Host Port 2 Encryption Switch Fabric Encryption Switch Virtual Target Virtual Initiator DEK Cluster Encryption Group Target Port 1 Target Port 2 Virtual Initiator Cluster Link Target Dedicated Cluster Network LAN Ciphertext Cleartext FIGURE 98 Single fabric deployment - DEK cluster Cluster Link 178 Fabric OS Encryption Administrator's Guide 53-1002159-03