Netgear FWAG114 FWAG114 Reference Manual - Page 159
Authentication and WEP Data Encryption
 |
UPC - 606449026955
View all Netgear FWAG114 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 159 highlights
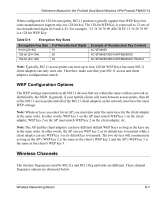
Reference Manual for the ProSafe Dual Band Wireless VPN Firewall FWAG114 The ESSID is usually broadcast in the air from an access point. The wireless station sometimes can be configured with the ESSID ANY. This means the wireless station will try to associate with whichever access point has the stronger radio frequency (RF) signal, providing that both the access point and wireless station use Open System authentication. Authentication and WEP Data Encryption The absence of a physical connection between nodes makes the wireless links vulnerable to eavesdropping and information theft. To provide a certain level of security, the IEEE 802.11 standard has defined these two types of authentication methods: • Open System. With Open System authentication, a wireless PC can join any network and receive any messages that are not encrypted. • Shared Key. With Shared Key authentication, only those PCs that possess the correct authentication key can join the network. By default, IEEE 802.11 wireless devices operate in an Open System network. Wired Equivalent Privacy (WEP) data encryption is used when the wireless devices are configured to operate in Shared Key authentication mode. 802.11 Authentication The 802.11 standard defines several services that govern how two 802.11 devices communicate. The following events must occur before an 802.11 Station can communicate with an Ethernet network through an access point such as the one built in to the FWAG114: 1. Turn on the wireless station. 2. The station listens for messages from any access points that are in range. 3. The station finds a message from an access point that has a matching SSID. 4. The station sends an authentication request to the access point. 5. The access point authenticates the station. 6. The station sends an association request to the access point. 7. The access point associates with the station. 8. The station can now communicate with the Ethernet network through the access point. Wireless Networking Basics D-3