Netgear FWAG114 FWAG114 Reference Manual - Page 176
VPN Tunnel
 |
UPC - 606449026955
View all Netgear FWAG114 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 176 highlights
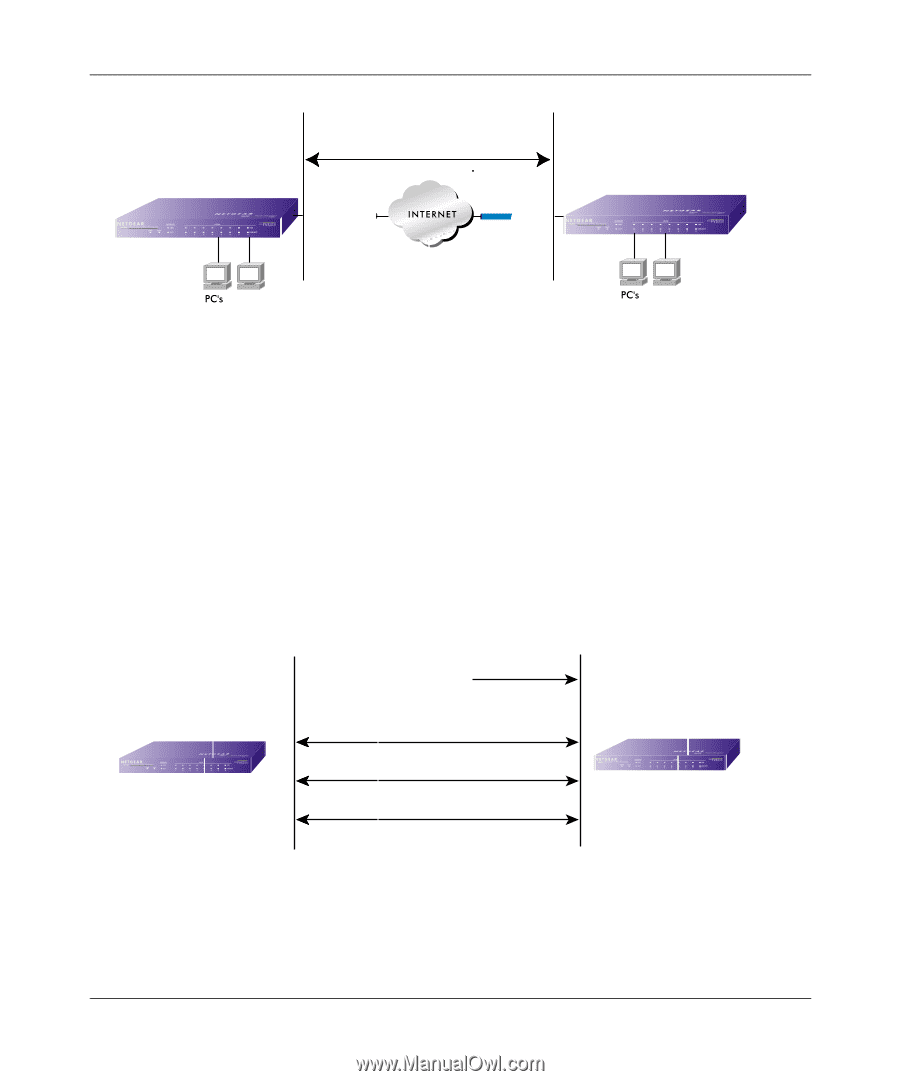
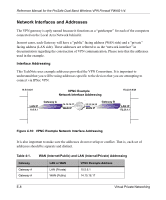
Reference Manual for the ProSafe Dual Band Wireless VPN Firewall FWAG114 VPN Gateway A VPN Tunnel VPN Gateway B Figure 4-11: VPN Tunnel SA The SA contains all the information necessary for gateway A to negotiate a secure and encrypted communication stream with gateway B. This communication is often referred to as a "tunnel." The gateways contain this information so that it does not have to be loaded onto every computer connected to the gateways. Each gateway must negotiate its Security Association with another gateway using the parameters and processes established by IPSec. As illustrated below, the most common method of accomplishing this process is via the Internet Key Exchange (IKE) protocol which automates some of the negotiation procedures. Alternatively, you can configure your gateways using manual key exchange, which involves manually configuring each paramter on both gateways. VPN Gateway IPSec Security Association IKE VPN Tunnel Negotiation Steps 1) Communication request sent to VPN Gateway 2) IKE Phase I authentication VPN Gateway 3) IKE Phase II negotiation 4) Secure data transfer 5) IPSec tunnel termination Figure 4-12: IPSec SA negotiation 1. The IPSec software on Host A initiates the IPSec process in an attempt to communicate with Host B. The two computers then begin the Internet Key Exchange (IKE) process. E-10 Virtual Private Networking