TP-Link TL-SG3216 TL-SG3216 V1 User Guide - Page 162
TP-Link TL-SG3216 Manual
 |
View all TP-Link TL-SG3216 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 162 highlights
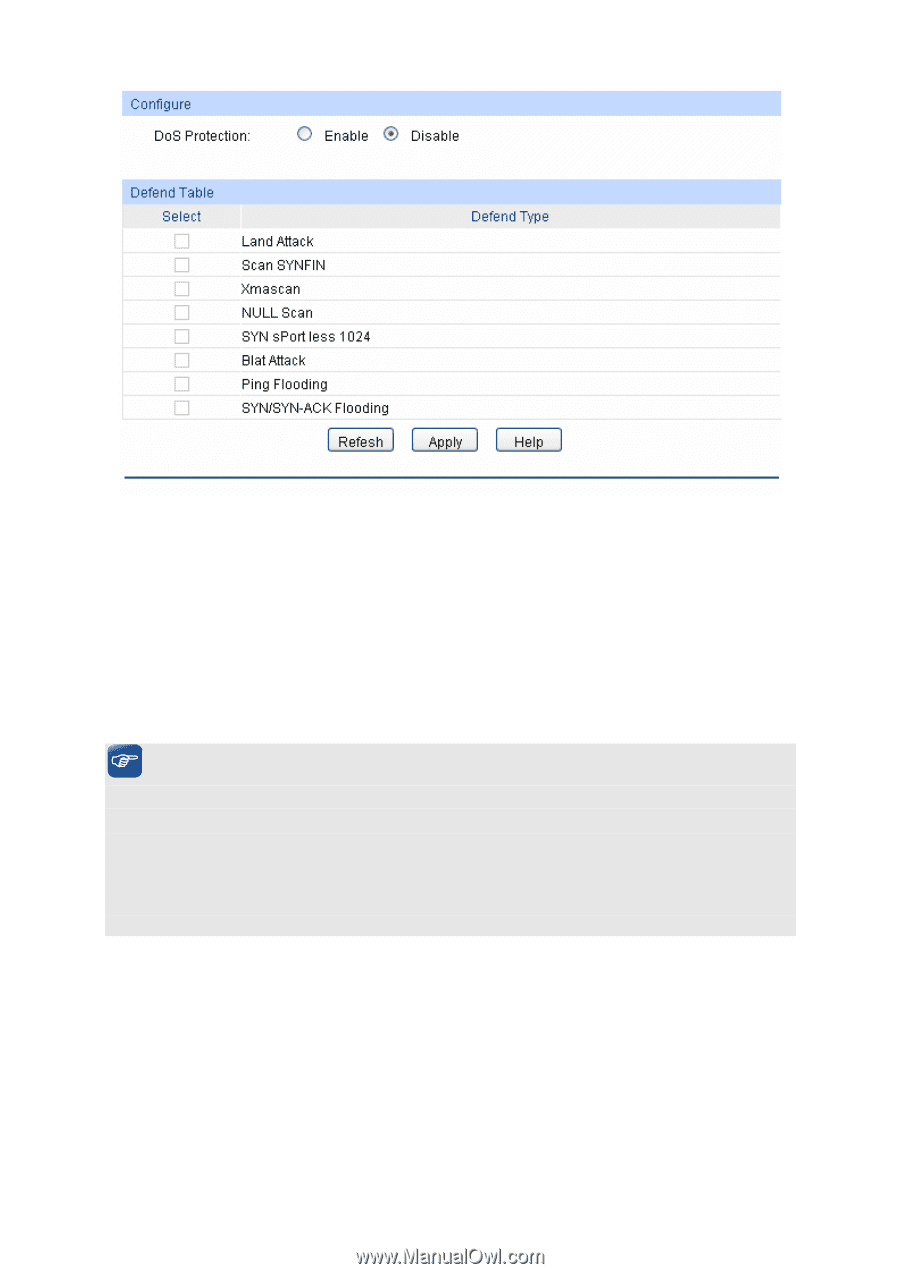
Figure 11-16 DoS Defend The following entries are displayed on this screen: ¾ Configure DoS Defend: Enable/Disable DoS Defend function. ¾ Defend Table Select: Select the entry to enable the corresponding Defend Type. Defend Type: Displays the Defend Type name. Tips: You are suggested to take the following further steps to ensure the network security. 1. It's recommended to inspect and repair the system vulnerability regularly. It is also necessary to install the system bulletins and backup the important information in time. 2. The network administrator is suggested to inspect the physic environment of the network and block the unnecessary network services. 3. Enhance the network security via the protection devices, such as the hardware firewall. 11.4 802.1X The 802.1X protocol was developed by IEEE802 LAN/WAN committee to deal with the security issues of wireless LANs. It was then used in Ethernet as a common access control mechanism for LAN ports to solve mainly authentication and security problems. 802.1X is a port-based network access control protocol. It authenticates and controls devices requesting for access in terms of the ports of LAN access control devices. With the 802.1X protocol enabled, a supplicant can access the LAN only when it passes the authentication, whereas those failing to pass the authentication are denied when accessing the LAN. ¾ Architecture of 802.1X Authentication 155