Dell PowerVault TL4000 Dell PowerVault ML6000 Encryption Key Manager User's - Page 13
Tape Encryption Overview, Components
 |
View all Dell PowerVault TL4000 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 13 highlights
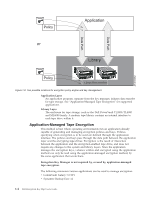
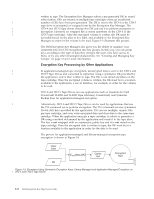
Chapter 1. Tape Encryption Overview Data is one of the most highly valued resources in a competitive business environment. Protecting that data, controlling access to it, and verifying its authenticity while maintaining its availability are priorities in our security-conscious world. Data encryption is a tool that answers many of these needs. The Dell Encryption Key Manager (referred to as the Encryption Key Manager from this point forward) simplifies encryption tasks. | The LTO 4 and LTO 5 drives are capable of encrypting data as it is written to any | LTO 4 and LTO 5 Data Cartridges. This new capability adds a strong measure of security to stored data without the processing overhead and performance degradation associated with encryption performed on the server or the expense of a dedicated appliance. The tape drive encryption solution comprises three major elements: The Encryption-Enabled Tape Drive | All LTO 4 and LTO 5 Tape Drives must be enabled through the library | interface. See "Hardware and Software Requirements" on page 2-2 for more information on tape drives. Encryption Key Management Encryption involves the use of several kinds of keys, in successive layers. The generation, maintenance, control, and transmission of these keys depends upon the operating environment where the encrypting tape drive is installed. Some applications are capable of performing key management. For environments without such applications or those where application-agnostic encryption is desired, Dell Encryption Key Manager performs all necessary key management tasks. "Managing Encryption" on page 1-2 describes these tasks in more detail. Encryption Policy This is the method used to implement encryption. It includes the rules that govern which volumes are encrypted and the mechanism for key selection. How and where these rules are set up depends on the operating environment. See "Managing Encryption" on page 1-2 for more information. Components The Encryption Key Manager is part of the Java environment and uses the Java Security components for its cryptographic capabilities. (For more information on the Java Security components please see the related publications section.) The Encryption Key Manager has three main components that are used to control its behavior. These components are: Java security keystore The keystore is defined as part of the Java Cryptography Extension (JCE) and an element of the Java Security components, which are, in turn, part of the Java runtime environment. A keystore holds the certificates and keys (or pointers to the certificates and keys) used by the Encryption Key Manager to perform cryptographic operations. Several types of Java keystores are supported offering different operational characteristics to meet your needs. These characteristics are discussed in detail in "Keystore 1-1