Dell PowerVault TL4000 Dell PowerVault ML6000 Encryption Key Manager User's - Page 23
Windows Solution Components, Keystore Considerations, The JCEKS Keystore, Tape Drive - service password
 |
View all Dell PowerVault TL4000 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 23 highlights
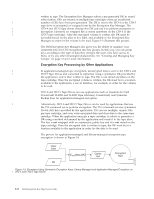
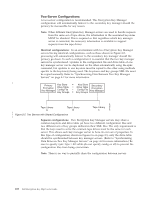
Tape Drive | For the LTO 4 and LTO 5 Tape Drives, assure that the firmware level is the latest | available. For firmware updates, visit http://support.dell.com. Windows Solution Components Operating Systems | Windows Server 2003, 2008, and 2008 R2 Dell Encryption Key Manager The minimum required version of the Encryption Key Manager is 2.1 with a build date of 20070914 or later, and one of the following IBM Runtime Environments: Table 2-2. Minimum Software Requirements for Windows Operating System IBM Runtime Environment Windows 2003 v IBM® 64-bit Runtime Environment for Windows on AMD64/EM64T architecture, Java 2 Technology Edition, Version 5.0 SR5 v IBM 32-bit Runtime Environment for Windows, Java 2 Technology Edition, Version 5.0 SR5 | Windows 2008 IBM 64-bit Runtime Environment for Windows on AMD64/EM64T | and 2008 R2 architecture, Java 2 Technology Edition, Version 6.0 SR5 Tape Libraries | For the Dell™ PowerVault™ TL2000 Tape Library, Dell™ PowerVault™ TL4000 Tape | Library, and Dell™ PowerVault™ ML6000 Tape Library, assure that the firmware | level is the latest available. For firmware update, visit http://support.dell.com. Tape Drive | For the LTO 4 and LTO 5 Tape Drives, assure that the firmware level is the latest | available. For firmware update, visit http://support.dell.com. Keystore Considerations It is impossible to overstate the importance of preserving your keystore data. Without access to your keystore you will be unable to decrypt your encrypted tapes. Carefully read the topics below to understand the methods available for protecting your keystore data. The JCEKS Keystore EKM supports the JCEKS keystore type. JCEKS (Unix System Services file based) is a file-based keystore supported on all platforms where EKM runs. Thus it is relatively easy to copy the contents of this keystore for back up and recovery, and to keep two EKM instances synchronized for failover. JCEKS provides password-based protection of the contents of the keystore for security, and provides relatively good performance. File copy methods such as FTP may be used. Chapter 2. Planning Your Encryption Key Manager Environment 2-3