Dell PowerVault TL4000 Dell PowerVault ML6000 Encryption Key Manager User's - Page 29
Disaster Recovery Site Considerations, Considerations for Sharing Encrypted Tapes Offsite
 |
View all Dell PowerVault TL4000 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 29 highlights
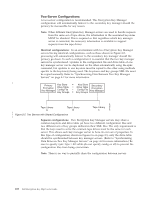
| Primary Key Store = Key Store Secondary Encryption Drive Table = Drive Table Encryption = Key Manager Config File Key Groups Config File Key Manager Key Groups a14m0255 Tape Library Tape Library Tape Library A B C | | Figure 2-6. Two Servers with Different Configurations Accessing the Same Devices | Disaster Recovery Site Considerations If you plan to use a disaster recovery (DR) site, the Encryption Key Manager provides a number of options to enable that site to read and write encrypted tapes. These are: v Create a duplicate Encryption Key Manager at the DR site. Set up a duplicate Encryption Key Manager at the DR site with the same information as your local Encryption Key Manager (configuration file, tape drive table, key groups XML file, and keystore). This key manager would then be in place and capable of taking over for one of your existing production key managers to read and write encrypted tapes. v Create a backup copy of the three Encryption Key Manager data files to be able to recover as needed. If you create a current copy of the four data elements needed by the Encryption Key Manager (configuration file, tape drive table, key groups XML file, and keystore) then you would be able to start a key manager at any time to act as a duplicate at the DR site. (Remember that you should not use the Encryption Key Manager to encrypt the copies of these files as you would not be able to decrypt it without a functioning key manager). If your DR site uses different tape drives from your primary site, the configuration file and tape drive table must contain the correct information for the DR site. Considerations for Sharing Encrypted Tapes Offsite Note: It is important to verify the validity of any certificate received from a business partner by checking the chain of trust of such a certificate back to the Certificate Authority (CA) that ultimately signed it. If you trust the CA, then you can trust that certificate. Alternately, the validity of a certificate can be verified if it was securely guarded in transit. Failure to verify a certificate's validity in one of these ways may open the door to a "Man-in-the-Middle" attack. | Sharing LTO 4 and LTO 5 Tape | In order to share encrypted data on an LTO 4 or LTO 5 tape, a copy of the symmetric key used to encrypt the data on the tape must be made available to the other organization to enable them to read the tape. In order for the symmetric key to be shared, the other organization must share their public key with you. This public key will be used to wrap the symmetric key when it is exported from the Encryption Key Manager keystore using keytool (see "Exporting Data Keys Using Chapter 2. Planning Your Encryption Key Manager Environment 2-9