Netgear MBRN3000 MBRN3000 User Manual - Page 18
Configuring WEP, WEP Wired Equivalent Privacy 128-bit encryption - support
 |
UPC - 606449068054
View all Netgear MBRN3000 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 18 highlights
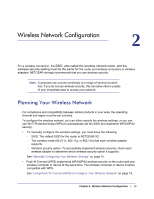
Mobile Broadband Wireless-N Router MBRN3000 Configuring WEP Note: If you use a wireless computer to configure wireless security settings, you will be disconnected when you click Apply. Reconfigure your wireless computer to match the new settings, or access the router from a wired computer to make further changes. To configure WEP data encryption: 1. Log in to the router as described in "Logging In to Your Router" on page 9. 2. From the main menu, select Wireless Settings to display the Wireless Settings screen. 3. In the Security Options section, select the WEP (Wired Equivalent Privacy) radio button: 4. Select the Authentication Type: Automatic, Open System, or Shared Key. The default is Open System. Note: The authentication is separate from the data encryption. You can select authentication that requires a shared key, but still leaves data transmissions unencrypted. Security is stronger if you use both the Shared Key and WEP encryption settings. 5. Select the Encryption Strength setting: • WEP (Wired Equivalent Privacy) 64-bit encryption. Enter 10 hexadecimal digits (any combination of 0-9, a-f, or A-F). • WEP (Wired Equivalent Privacy) 128-bit encryption. Enter 26 hexadecimal digits (any combination of 0-9, a-f, or A-F). 6. Enter the encryption keys. You can manually or automatically program the four data encryption keys. These values must be identical on all computers and Access Points in your network: • Passphrase. To use a passphrase to generate the keys, enter a passphrase, and click Generate. This automatically creates the keys. Wireless stations must use the passphrase or keys to access the router. Note: Not all wireless adapters support passphrase key generation. • Key 1-Key4. These values are not case-sensitive. You can manually enter the four data encryption keys. These values must be identical on all computers and access 18 | Chapter 2: Wireless Network Configuration