HP 6125XLG R2306-HP 6125XLG Blade Switch Security Command Reference - Page 79
secondary authorization, cipher, simple, vpn-instance, ipv4-address, port-number, string
 |
View all HP 6125XLG manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 79 highlights
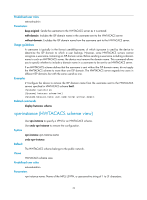
Syntax secondary authorization { ipv4-address | ipv6 ipv6-address } [ port-number I key { cipher | simple } string | vpn-instance vpn-instance-name ] * undo secondary authorization [ { ipv4-address | ipv6 ipv6-address } [ port-number | vpn-instance vpn-instance-name ]* ] Default No secondary HWTACACS authorization server is specified. Views HWTACACS scheme view Predefined user roles network-admin Parameters ipv4-address: Specifies the IPv4 address of the secondary HWTACACS authorization server. ipv6 ipv6-address: Specifies the IPv6 address of the secondary HWTACACS authorization server. port-number: Specifies the service port number of the secondary HWTACACS authorization server, a TCP port number in the range of 1 to 65535. The default setting is 49. key { cipher | simple } string: Sets the shared key for secure communication with the secondary HWTACACS authorization server. • cipher string: Sets a ciphertext shared key. The string argument is case sensitive. { In non-FIPS mode, the key is a string of 1 to 373 characters. { In FIPS mode, the key is a string of 15 to 373 characters. • simple string: Sets a plaintext shared key. The string argument is case sensitive. { In non-FIPS mode, the key is a string of 1 to 255 characters. { In FIPS mode, the key is a string of 15 to 255 characters and must contain numbers, uppercase letters, lowercase letters, and special characters. vpn-instance vpn-instance-name: Specifies the MPLS L3VPN to which the secondary HWTACACS authorization server belongs, where vpn-instance-name is a case-sensitive string of 1 to 31 characters. If the server is on the public network, do not specify this option. Usage guidelines Make sure that the port number and shared key settings of the secondary HWTACACS authorization server are the same as those configured on the server. You can configure up to 16 secondary HWTACACS authorization servers for an HWTACACS scheme. With the configuration, if the primary server fails, the device looks for a secondary server in active state (a secondary HWTACACS authorization server configured earlier has a higher priority) and tries to communicate with it. If you use the undo secondary authorization command without specifying any parameter, the command removes all secondary authorization servers. Two authorization servers specified for a scheme, primary or secondary, cannot have identical IP address, port number, and VPN settings. 70