D-Link DES-3028 Product Manual - Page 215
X Port-based Access Control, Example of Typical Port-Based Configuration
 |
UPC - 790069305375
View all D-Link DES-3028 manuals
Add to My Manuals
Save this manual to your list of manuals |
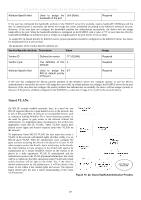
Page 215 highlights
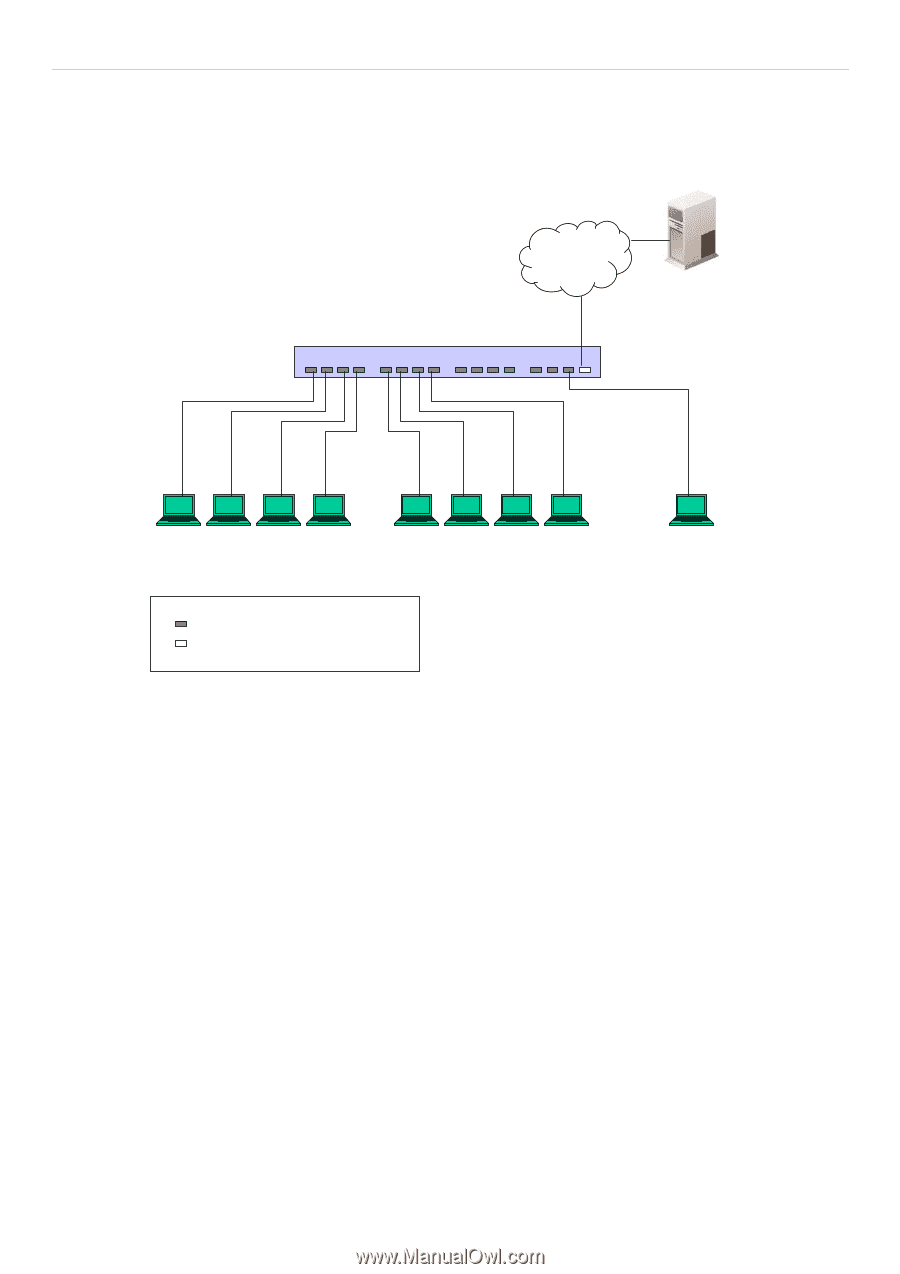
DES-3028 DES-3028P DES-3028G DES-3052 DES-3052P Layer 2 Fast Ethernet Managed Switch detects events that indicate the attachment of an active device at the remote end of the link, or an active device becoming inactive. These events can be used to control the authorization state of the Port and initiate the process of authenticating the attached device if the Port is unauthorized. This is the Port-Based Network Access Control. 802.1X Port-based Access Control Ethernet Switch RADIUS Server 802.1X Client 802.1X 802.1X 802.1X Client Client Client 802.1X Client 802.1X Client 802.1X Client ... 802.1X Client 802.1X Client Network access controlled port Network access uncontrolled port Figure 10- 20. Example of Typical Port-Based Configuration Once the connected device has successfully been authenticated, the Port then becomes Authorized, and all subsequent traffic on the Port is not subject to access control restriction until an event occurs that causes the Port to become Unauthorized. Hence, if the Port is actually connected to a shared media LAN segment with more than one attached device, successfully authenticating one of the attached devices effectively provides access to the LAN for all devices on the shared segment. Clearly, the security offered in this situation is open to attack. 201