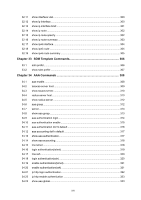
23.1
port isolation
...........................................................................................................
174
23.2
show port isolation interface
...................................................................................
175
Chapter 24
Loopback Detection Commands
....................................................
176
24.1
loopback-detection(global)
.....................................................................................
176
24.2
loopback-detection interval
.....................................................................................
176
24.3
loopback-detection recovery-time
..........................................................................
177
24.4
loopback-detection(interface)
.................................................................................
178
24.5
loopback-detection config
.......................................................................................
178
24.6
loopback-detection recover
....................................................................................
179
24.7
show loopback-detection global
.............................................................................
180
24.8
show loopback-detection interface
.........................................................................
180
Chapter 25
ACL Commands
...............................................................................
182
25.1
time-range
...............................................................................................................
182
25.2
absolute
..................................................................................................................
182
25.3
periodic
...................................................................................................................
183
25.4
holiday
....................................................................................................................
184
25.5
holiday(global)
........................................................................................................
185
25.6
access-list create
....................................................................................................
185
25.7
mac access-list
.......................................................................................................
186
25.8
access-list standard
................................................................................................
186
25.9
access-list extended
...............................................................................................
188
25.10
access-list ipv6
.......................................................................................................
189
25.11
rule
..........................................................................................................................
190
25.12
access-list policy name
...........................................................................................
191
25.13
access-list policy action
..........................................................................................
192
25.14
redirect interface
.....................................................................................................
192
25.15
s-condition
..............................................................................................................
193
25.16
s-mirror
...................................................................................................................
194
25.17
qos-remark
..............................................................................................................
194
25.18
access-list bind acl(interface)
.................................................................................
195
25.19
access-list bind acl(vlan)
........................................................................................
196
25.20
access-list bind(interface)
.......................................................................................
196
25.21
access-list bind(vlan)
..............................................................................................
197
25.22
show access-list
.....................................................................................................
197
25.23
show access-list policy
...........................................................................................
198
25.24
show access-list bind
..............................................................................................
198
IX