Lenovo ThinkPad 770 ThinkPad 770 User's Guide - Page 105
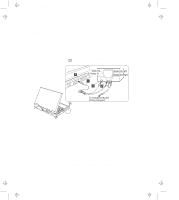
Using the Security System Lock, Device Manager
 |
View all Lenovo ThinkPad 770 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 105 highlights
Title: C79DMMST CreationDate: 07/16/97 13:09:22 3. Click on Device Manager and check whether there is a resource conflict between the new IDE device and the other devices in the computer. If there is a resource conflict, go to "Resolving System Resource Conflicts" in the online book. Using the Security System Lock To prevent your computer from being stolen, you should purchase the optional security system lock from your dealer. You will be responsible for its evaluation, selection, and installation. IBM will not be held responsible for its functionality, quality, or performance. Refer to the instructions shipped with this option for how to use this security feature. Chapter 3. Installing Options 3-21

3. Click on
Device Manager
and check whether there is a resource
conflict between the new IDE device and the other devices in the
computer.
If there is a resource conflict, go to “Resolving
System Resource Conflicts” in the online book.
Using the Security System Lock
To prevent your computer from being stolen, you should purchase
the optional security system lock from your dealer.
You will be
responsible for its evaluation, selection, and installation.
IBM will not
be held responsible for its functionality, quality, or performance.
Refer to the instructions shipped with this option for how to use this
security feature.
Chapter 3.
Installing Options
3-21
Title: C79DMMST CreationDate: 07/16/97 13:09:22