ZyXEL UAG4100 User Guide - Page 353
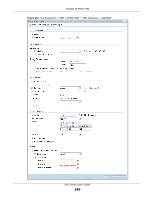
Configuration > VPN > IPSec VPN > VPN Gateway > Add/Edit continued
 |
View all ZyXEL UAG4100 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 353 highlights
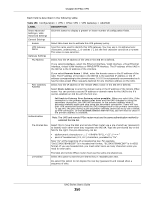
Chapter 30 IPSec VPN Table 158 Configuration > VPN > IPSec VPN > VPN Gateway > Add/Edit (continued) LABEL Encryption DESCRIPTION Select which key size and encryption algorithm to use in the IKE SA. Choices are: DES - a 56-bit key with the DES encryption algorithm 3DES - a 168-bit key with the DES encryption algorithm AES128 - a 128-bit key with the AES encryption algorithm AES192 - a 192-bit key with the AES encryption algorithm AES256 - a 256-bit key with the AES encryption algorithm Authentication The UAG and the remote IPSec router must use the same key size and encryption algorithm. Longer keys require more processing power, resulting in increased latency and decreased throughput. Select which hash algorithm to use to authenticate packet data in the IPSec SA. Choices are SHA1, SHA256, SHA512 and MD5. SHA is generally considered stronger than MD5, but it is also slower. Key Group The remote IPSec router must use the same authentication algorithm. Select which Diffie-Hellman key group (DHx) you want to use for encryption keys. Choices are: DH1 - use a 768-bit random number DH2 - use a 1024-bit random number DH5 - use a 1536-bit random number NAT Traversal The longer the key, the more secure the encryption, but also the longer it takes to encrypt and decrypt information. Both routers must use the same DH key group. Select this if any of these conditions are satisfied. Dead Peer Detection (DPD) • This IKE SA might be used to negotiate IPSec SAs that use ESP as the active protocol. • There are one or more NAT routers between the UAG and remote IPSec router, and these routers do not support IPSec pass-thru or a similar feature. The remote IPSec router must also enable NAT traversal, and the NAT routers have to forward packets with UDP port 500 and UDP 4500 headers unchanged. Select this check box if you want the UAG to make sure the remote IPSec router is there before it transmits data through the IKE SA. The remote IPSec router must support DPD. If there has been no traffic for at least 15 seconds, the UAG sends a message to the remote IPSec router. If the remote IPSec router responds, the UAG transmits the data. If the remote IPSec router does not respond, the UAG shuts down the IKE SA. X-Auth Enable Extended Authentication Server Mode Client Mode If the remote IPSec router does not support DPD, see if you can use the VPN connection connectivity check (see Section 30.2.1 on page 341). When multiple IPSec routers use the same VPN tunnel to connect to a single VPN tunnel (telecommuters sharing a tunnel for example), use extended authentication to enforce a user name and password check. This way even though they all know the VPN tunnel's security settings, each still has to provide a unique user name and password. Select this if one of the routers (the UAG or the remote IPSec router) verifies a user name and password from the other router using the local user database and/or an external server. Select this if the UAG authenticates the user name and password from the remote IPSec router. You also have to select the authentication method, which specifies how the UAG authenticates this information. Select this radio button if the UAG provides a username and password to the remote IPSec router for authentication. You also have to provide the User Name and the Password. UAG Series User's Guide 353