Symantec 14541094 Administration Guide - Page 97
Protecting session security, Web-based authentication types, Session security options
 |
UPC - 037648640480
View all Symantec 14541094 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 97 highlights
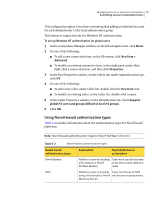
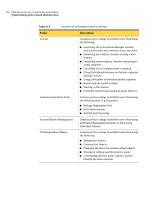
Managing security in Symantec pcAnywhere 97 Protecting session security Table 6-3 Web-based authentication types (continued) Web-based authentication Explanation methods Implementation in pcAnywhere Netscape LDAP Caller Authentication Validates a user by checking a list stored in an LDAP 3.0-compliant directory service. Users must log on to the LDAP server, and then they can browse for user names. Protecting session security Symantec pcAnywhere provides a number of options to protect the privacy of a session and prevent users from performing specific tasks that might interfere with the host session. These security measures provide an additional layer of security, but are most effective when used in combination with stronger security features in pcAnywhere. These measures include authentication and encryption, which are designed to protect the host from unauthorized access and intentional disruption of service. Table 6-4 includes information about the ways in which pcAnywhere can protect session security. Table 6-4 Session security options Option Description Strong encryption Protect the data stream, including the authorization process, from eavesdropping and hacker attacks by using strong encryption. Symantec pcAnywhere supports public-key and symmetric types of strong encryption. When connecting with a host or remote that is running pcAnywhere 11.0.x or earlier, either user can deny a connection if the other is using a lower level of encryption. If the connection is not denied, pcAnywhere automatically lowers the encryption of the computer with the higher encryption level to match the encryption of the computer with the lower encryption level. When both the host and remote are running pcAnywhere 11.5 or later, pcAnywhere automatically raises the encryption of the computer with the lower encryption level to match the encryption of the computer with the higher encryption level.