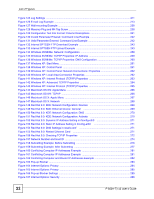
List of Figures
P-660H-Tx v2 User’s Guide
20
Figure 39 Traffic Redirect Example
........................................................................................................
81
Figure 40 Traffic Redirect LAN Setup
.....................................................................................................
82
Figure 41 WAN Backup Setup
................................................................................................................
82
Figure 42 LAN and WAN IP Addresses
..................................................................................................
85
Figure 43 Any IP Example
......................................................................................................................
89
Figure 44 LAN IP
....................................................................................................................................
90
Figure 45 Advanced LAN Setup
.............................................................................................................
91
Figure 46 DHCP Setup
...........................................................................................................................
92
Figure 47 LAN Client List
........................................................................................................................
93
Figure 48 Physical Network & Partitioned Logical Networks
..................................................................
94
Figure 49 LAN IP Alias
...........................................................................................................................
95
Figure 50 How NAT Works
.....................................................................................................................
98
Figure 51 NAT Application With IP Alias
................................................................................................
99
Figure 52 NAT General
........................................................................................................................
101
Figure 53 Multiple Servers Behind NAT Example
................................................................................
103
Figure 54 NAT Port Forwarding
............................................................................................................
104
Figure 55 Port Forwarding Rule Setup
................................................................................................
105
Figure 56 Address Mapping Rules
.......................................................................................................
106
Figure 57 Edit Address Mapping Rule
.................................................................................................
107
Figure 58 Firewall Application
...............................................................................................................
113
Figure 59 Three-Way Handshake
..........................................................................................................
114
Figure 60 SYN Flood
.............................................................................................................................
115
Figure 61 Smurf Attack
..........................................................................................................................
115
Figure 62 Stateful Inspection
.................................................................................................................
117
Figure 63 Firewall: General
..................................................................................................................
126
Figure 64 Firewall Rules
......................................................................................................................
128
Figure 65 Firewall: Edit Rule
................................................................................................................
130
Figure 66 Firewall: Customized Services
.............................................................................................
132
Figure 67 Firewall: Configure Customized Services
.............................................................................
133
Figure 68 Firewall Example: Rules
.......................................................................................................
134
Figure 69 Edit Custom Port Example
...................................................................................................
134
Figure 70 Firewall Example: Edit Rule: Destination Address
..............................................................
135
Figure 71 Firewall Example: Edit Rule: Select Customized Services
...................................................
136
Figure 72 Firewall Example: Rules: MyService
...................................................................................
137
Figure 73 Firewall: Anti Probing
...........................................................................................................
139
Figure 74 Firewall: Threshold
...............................................................................................................
142
Figure 75 Content Filter: Keyword
........................................................................................................
146
Figure 76 Content Filter: Schedule
.......................................................................................................
147
Figure 77 Content Filter: Trusted
..........................................................................................................
148
Figure 78 Example of Static Routing Topology
.....................................................................................
151
Figure 79 Static Route
..........................................................................................................................
152
Figure 80 Static Route Edit
...................................................................................................................
153
Figure 81 Subnet-based Bandwidth Management Example
................................................................
156