ZyXEL P-660H-T1 v2 User Guide - Page 214
Table 80, Table 81, Table 79
 |
View all ZyXEL P-660H-T1 v2 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 214 highlights
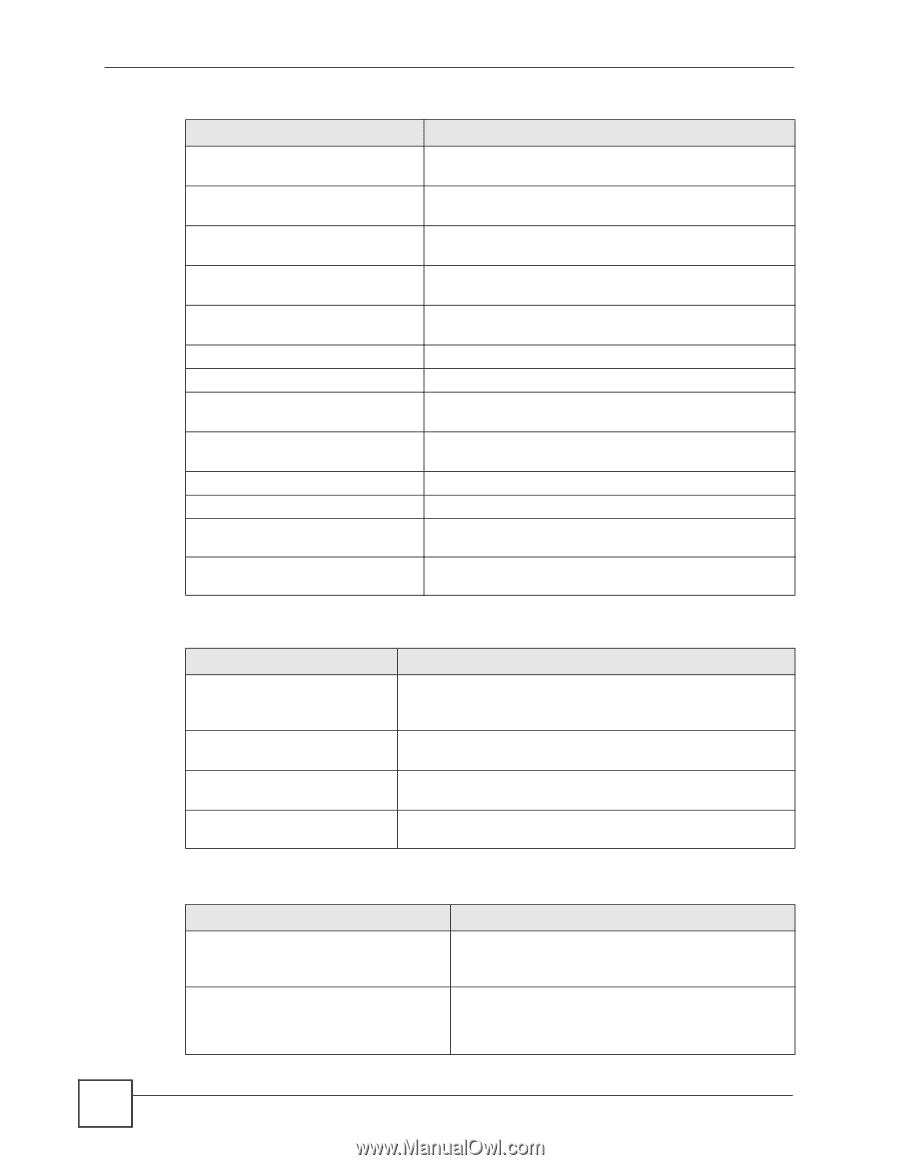
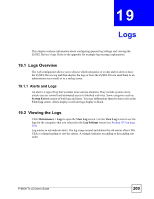
Chapter 19 Logs Table 79 System Maintenance Logs (continued) LOG MESSAGE DESCRIPTION Starting Connectivity Monitor Starting Connectivity Monitor. Time initialized by Daytime The router got the time and date from the Daytime server. Server Time initialized by Time server The router got the time and date from the time server. Time initialized by NTP server The router got the time and date from the NTP server. Connect to Daytime server fail The router was not able to connect to the Daytime server. Connect to Time server fail The router was not able to connect to the Time server. Connect to NTP server fail The router was not able to connect to the NTP server. Too large ICMP packet has been dropped The router dropped an ICMP packet that was too large. Configuration Change: PC = 0x%x, Task ID = 0x%x The router is saving configuration changes. Successful SSH login Someone has logged on to the router's SSH server. SSH login failed Someone has failed to log on to the router's SSH server. Successful HTTPS login Someone has logged on to the router's web configurator interface using HTTPS protocol. HTTPS login failed Someone has failed to log on to the router's web configurator interface using HTTPS protocol. Table 80 System Error Logs LOG MESSAGE %s exceeds the max. number of session per host! setNetBIOSFilter: calloc error readNetBIOSFilter: calloc error WAN connection is down. DESCRIPTION This attempt to create a NAT session exceeds the maximum number of NAT session table entries allowed to be created per host. The router failed to allocate memory for the NetBIOS filter settings. The router failed to allocate memory for the NetBIOS filter settings. A WAN connection is down. You cannot access the network through this interface. Table 81 Access Control Logs LOG MESSAGE Firewall default policy: [TCP | UDP | IGMP | ESP | GRE | OSPF] Firewall rule [NOT] match:[TCP | UDP | IGMP | ESP | GRE | OSPF] , DESCRIPTION Attempted TCP/UDP/IGMP/ESP/GRE/OSPF access matched the default policy and was blocked or forwarded according to the default policy's setting. Attempted TCP/UDP/IGMP/ESP/GRE/OSPF access matched (or did not match) a configured firewall rule (denoted by its number) and was blocked or forwarded according to the rule. 214 P-660H-Tx v2 User's Guide