Netgear DG834Gv1 DG834Gv2 Reference Manual - Page 209
Overview of WEP Parameters, Do Not Use WEP, Use WEP for Encryption
 |
View all Netgear DG834Gv1 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 209 highlights
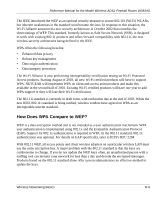
Reference Manual for the Model Wireless ADSL Firewall Router DG834G 802.11b Authentication Shared Key Steps 1) Authentication request sent to AP 2) AP sends challenge text Client 3) Client encrypts attempting challenge text and to connect sends it back to AP Access Point Router Cable/DSL ProSafeWirelessVPN Security Firewall PWR TEST IN TER N ET LNK W LA N LO CA L MODEL FVM318 100 ACT Enable LNK/ACT 1 2 3 4 5 6 7 8 4) AP decrypts, and if correct, authenticates client 5) Client connects to network Figure D-2: Shared key authentication Overview of WEP Parameters Before enabling WEP on an 802.11 network, you must first consider what type of encryption you require and the key size you want to use. Typically, there are three WEP Encryption options available for 802.11 products: 1. Do Not Use WEP: The 802.11 network does not encrypt data. For authentication purposes, the network uses Open System Authentication. 2. Use WEP for Encryption: A transmitting 802.11 device encrypts the data portion of every packet it sends using a configured WEP Key. The receiving device decrypts the data using the same WEP Key. For authentication purposes, the network uses Open System Authentication. 3. Use WEP for Authentication and Encryption: A transmitting 802.11 device encrypts the data portion of every packet it sends using a configured WEP Key. The receiving device decrypts the data using the same WEP Key. For authentication purposes, the wireless network uses Shared Key Authentication. Note: Some 802.11 access points also support Use WEP for Authentication Only (Shared Key Authentication without data encryption). Wireless Networking Basics D-5