Netgear DG834Gv1 DG834Gv2 Reference Manual - Page 66
Inbound Rules (Port Forwarding), Inbound Rule Example: A Local Public Web Server
 |
View all Netgear DG834Gv1 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 66 highlights
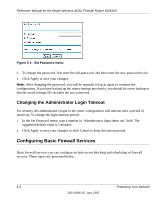
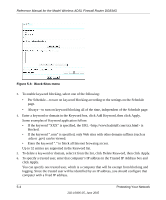
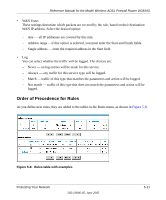
Reference Manual for the Model Wireless ADSL Firewall Router DG834G • To edit an existing rule, select its button on the left side of the table and click Edit. • To delete an existing rule, select its button on the left side of the table and click Delete. • To move an existing rule to a different position in the table, select its button on the left side of the table and click Move. At the script prompt, enter the number of the desired new position and click OK. Inbound Rules (Port Forwarding) Because the DG834G uses Network Address Translation (NAT), your network presents only one IP address to the Internet, and outside users cannot directly address any of your local computers. However, by defining an inbound rule you can make a local server (for example, a Web server or game server) visible and available to the Internet. The rule tells the router to direct inbound traffic for a particular service to one local server based on the destination port number. This is also known as port forwarding. Note: Some residential broadband ISP accounts do not allow you to run any server processes (such as a Web or FTP server) from your location. Your ISP may periodically check for servers and may suspend your account if it discovers any active services at your location. If you are unsure, refer to the Acceptable Use Policy of your ISP. Remember that allowing inbound services opens holes in your firewall. Only enable those ports that are necessary for your network. Following are two application examples of inbound rules: Inbound Rule Example: A Local Public Web Server If you host a public Web server on your local network, you can define a rule to allow inbound Web (HTTP) requests from any outside IP address to the IP address of your Web server at any time of day. This rule is shown in Figure 5-5: 5-6 Protecting Your Network 202-10006-05, June 2005