Netgear DG834G DG834Gv5 Reference Manual - Page 130
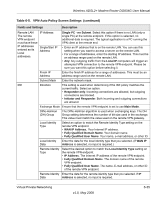
Virtual Private Networking, SHA-1, Fields and Settings, Description
 |
UPC - 606449029918
View all Netgear DG834G manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 130 highlights
Wireless ADSL2+ Modem Router DG834G User Manual Table 6-5. VPN-Auto Policy Screen Settings (continued) Fields and Settings Description Parameters Encryption Algorithm The encryption algorithm used for both IKE and IPSec. This setting must match the setting used on the remote VPN Gateway. DES and 3DES are supported. • DES. The Data Encryption Standard (DES) processes input data that is 64 bits wide, encrypting these values using a 56-bit key. Faster but less secure than 3DES. • 3DES. (Triple DES) achieves a higher level of security by encrypting the data three times using DES with three different, unrelated keys. Authentication Algorithm Pre-shared key The authentication algorithm used for both IKE and IPSec. This setting must match the setting used on the remote VPN Gateway. Auto, MD5, and SHA-1 are supported. Auto negotiates with the remote VPN endpoint and is not available in responder-only mode. • MD5. 128 bits, faster but less secure. • SHA-1. (default)160 bits, slower but more secure. This is the default. The key must be entered both here and on the remote VPN Gateway. SA Life Time Enable IPSec PFS (Perfect Forward Secrecy) This determines the time interval before the SA (Security Association) expires. (It will automatically be re-established as required.) While using a short time period (or data amount) increases security, it also degrades performance. It is common to use periods over an hour (3600 seconds) for the SA Life Time. This setting applies to both IKE and IPSec SAs. • If this check box is selected, security is enhanced by ensuring that the key is changed at regular intervals. Also, even if one key is broken, subsequent keys are no easier to break. (Each key has no relationship to the previous key.) • This setting applies to both IKE and IPSec SAs. When configuring the remote endpoint to match this setting, you might have to specify the key group used. For this device, the key group is the same as the DH Group setting in the IKE section. 6-36 v1.0, May 2008 Virtual Private Networking