Netgear DG834G DG834Gv5 Reference Manual - Page 138
Table 6-7., VPN Manual Policy Fields and Settings, continued, Single PC - no Subnet, Local IP, SHA-1
 |
UPC - 606449029918
View all Netgear DG834G manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 138 highlights
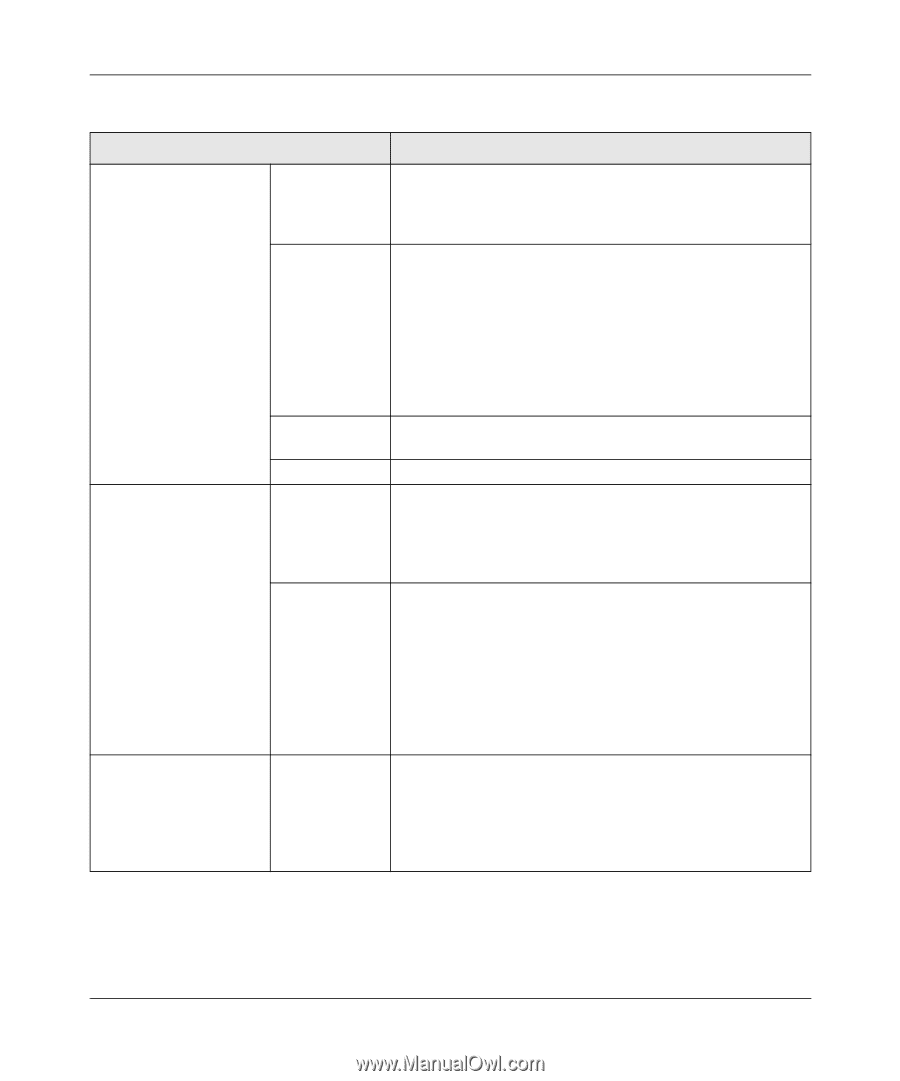
Wireless ADSL2+ Modem Router DG834G User Manual Table 6-7. VPN Manual Policy Fields and Settings (continued) Fields and Settings Remote LAN The remote VPN endpoint must have these IP addresses entered as its Local addresses. IP Address Single/Start IP Address ESP Configuration ESP (Encapsulating Security Payload) provides security for the payload (data) sent through the VPN tunnel. Finish IP Address Subnet Mask SPI Encryption Authentication Description Single PC - no Subnet. Select this option if there is no LAN (only a single PC) at the remote endpoint. If this option is selected, no additional data is required. The typical application is a PC running the VPN client at the remote end. • Enter an IP address that is on the remote LAN. You can use this setting when you want to access a server on the remote LAN. • For a range of addresses, enter the starting IP address. This must be an address range used on the remote LAN. • Any. Any outgoing traffic from the Local IP computers will trigger an attempted VPN connection to the remote VPN endpoint. Please be sure you want this option before selecting it. Enter the finish IP address for a range of addresses. This must be an address range used on the remote LAN. Enter the network mask. Enter the required Security Policy Indexes (SPIs). Each policy must have unique SPIs. These settings must match the remote VPN endpoint. The in setting here must match the out setting on the remote VPN endpoint, and the out setting here must match the in setting on the remote VPN endpoint. Select an encryption algorithm, and enter the key in the field provided. For 3DES, the keys should be 24 ASCII characters and for DES, the keys should be 8 ASCII characters. • DES. The Data Encryption Standard (DES) processes input data that is 64 bits wide, encrypting these values using a 56 bit key. Faster but less secure than 3DES. • 3DES. (Triple DES) achieves a higher level of security by encrypting the data three times using DES with three different, unrelated keys. Select the SHA-1 or MD5 authentication algorithm, and enter the key in the field provided. For MD5, the keys should be 16 ASCII characters. For SHA-1, the keys should be 20 ASCII characters. • MD5. 128 bits, faster but less secure. • SHA-1. (default)160 bits, slower but more secure. 6-44 v1.0, May 2008 Virtual Private Networking