Symantec 10067161 Product Manual - Page 126
About Reputation Scan, Insight Protection, On/Off, Settings, Apply, Insight Network, Computer Scan
 |
UPC - 037648227964
View all Symantec 10067161 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 126 highlights
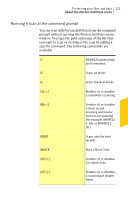
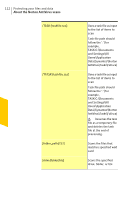
126 Protecting your files and data About the Norton AntiVirus scans 4 In the Insight Protection row, do one of the following: 1 To turn off Insight Protection, move the On/Off switch to the right to the Off position. 1 To turn on Insight Protection, move the On/Off switch to the left to the On position. 5 In the Settings window, click Apply. About Reputation Scan Reputation Scan provides information on the trust-worthiness of all programs and running processes on your computer. It helps you detect the files that are suspicious or vulnerable on your computer using the reputation-based threat detection. Norton AntiVirus lets you run different types of Reputation Scan and detect suspicious programs on your computer. Reputation Scan filters the files on the basis of certain filtering criteria and performs an Insight Network Scan on the filtered files. Reputation Scan filters the files as reputation files. It filters .exe files, .scr files, .sys files, .dll files, .drv files, .ocx files, .loc files, and .msi files and analyzes these files. When you perform a Reputation Quick Scan or Full System Scan, Norton AntiVirus considers the Files of Interest that are available on your computer. After it has filtered the reputation files, Norton AntiVirus performs an Insight Network Scan. When Norton AntiVirus performs an Insight Network Scan, it also performs a Computer Scan. Norton AntiVirus uses the Computer Scan to perform the signature-based threat detection. It compares the signature of the filtered reputation files against the known threat signatures to identify threats on your computer. If a security threat is detected, Norton AntiVirus automatically removes the threat from your computer. Norton AntiVirus uses the Insight Network Scan to detect suspicious or vulnerable files on your computer