Cisco NM-8B-U User Guide - Page 26
Understanding ACLs
 |
UPC - 074632001001
View all Cisco NM-8B-U manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 26 highlights
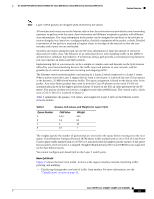
Feature Overview 16- and 36-Port Ethernet Switch Module for Cisco 2600 Series, Cisco 3600 Series, and Cisco 3700 Series Understanding ACLs Packet filtering can limit network traffic and restrict network use by certain users or devices. ACLs can filter traffic as it passes through a switch and permit or deny packets from crossing specified interfaces. An ACL is a sequential collection of permit and deny conditions that apply to packets. When a packet is received on an interface, the switch compares the fields in the packet against any applied ACLs to verify that the packet has the required permissions to be forwarded, based on the criteria specified in the access lists. The switch tests the packet against the conditions in an access list one by one. The first match determines whether the switch accepts or rejects the packet. Because the switch stops testing conditions after the first match, the order of conditions in the list is critical. If no conditions match, the switch rejects the packet. If there are no restrictions, the switch forwards the packet; otherwise, the switch drops the packet. You configure access lists on a Layer 2 switch to provide basic security for your network. If you do not configure ACLs, all packets passing through the switch could be allowed onto all parts of the network. You can use ACLs to control which hosts can access different parts of a network or to decide which types of traffic are forwarded or blocked at switch interfaces. For example, you can allow e-mail traffic to be forwarded but not Telnet traffic. ACLs can be configured to block inbound traffic. An ACL contains an ordered list of access control entries (ACEs). Each ACE specifies permit or deny and a set of conditions the packet must satisfy in order to match the ACE. The meaning of permit or deny depends on the context in which the ACL is used. The Ethernet switch network module supports IP ACLs to filter IP traffic, including TCP or User Datagram Protocol (UDP) traffic (but not both traffic types in the same ACL). ACLs You can apply ACLs on physical Layer 2 interfaces. ACLs are applied on interfaces only on the inbound direction. • Standard IP access lists use source addresses for matching operations. • Extended IP access lists use source and destination addresses and optional protocol type information for matching operations. The switch examines access lists associated with features configured on a given interface and a direction. As packets enter the switch on an interface, ACLs associated with all inbound features configured on that interface are examined. ACLs permit or deny packet forwarding based on how the packet matches the entries in the ACL. For example, you can use ACLs to allow one host to access a part of a network, but to prevent another host from accessing the same part. In Figure 13, ACLs applied at the switch input allow Host A to access the Human Resources network, but prevent Host B from accessing the same network. Cisco IOS Release 12.2(2)XT, 12.2(8)T, and 12.2(15)ZJ 26