Cisco NM-8B-U User Guide - Page 90
Configuring a QoS Policy, no mls qos cos, override, switchport priority, show mls qos interface
 |
UPC - 074632001001
View all Cisco NM-8B-U manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 90 highlights
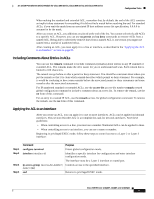
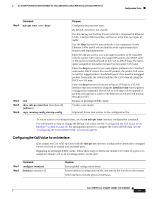
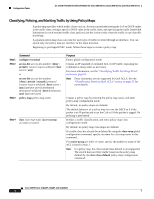
Configuration Tasks 16- and 36-Port Ethernet Switch Module for Cisco 2600 Series, Cisco 3600 Series, and Cisco 3700 Series Step 3 Step 4 Step 5 Step 6 Command mls qos cos {default-cos | override} end show mls qos interface copy running-config startup-config Purpose Configures the default CoS value for the port. For default-cos, specify a default CoS value to be assigned to a port. If the port is CoS trusted and packets are untagged, the default CoS value becomes the CoS value for the packet. The CoS range is 0 to 7. The default is 0. Use the override keyword to override the previously configured trust state of the incoming packets and to apply the default port CoS value to all incoming packets. By default, CoS override is disabled. Use the override keyword when all incoming packets on certain ports deserve higher priority than packets entering from other ports. Even if a port was previously set to trust DSCP, this command overrides the previously configured trust state, and all the incoming CoS values are assigned the default CoS value configured with this command. If an incoming packet is tagged, the CoS value of the packet is modified with the default CoS of the port at the ingress port. Returns to privileged EXEC mode. Verifies your entries. (Optional) Saves your entries in the configuration file. To return to the default setting, use the no mls qos cos {default-cos | override} interface configuration command. Note The mls qos cos command replaced the switchport priority command in Cisco IOS Release 12.1(6)EA2. Configuring a QoS Policy Configuring a QoS policy typically requires classifying traffic into classes, configuring policies applied to those traffic classes, and attaching policies to interfaces. For background information, see the "Classification" section on page 32 and the "Policing and Marking" section on page 34. This section contains this configuration information: • Classifying Traffic by Using ACLs, page 91 • Classifying Traffic by Using Class Maps, page 93 • Classifying, Policing, and Marking Traffic by Using Policy Maps, page 94 Cisco IOS Release 12.2(2)XT, 12.2(8)T, and 12.2(15)ZJ 90