ZyXEL ZyWALL 5 User Guide - Page 282
Intrusion Severity, Signature Actions
 |
View all ZyXEL ZyWALL 5 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 282 highlights
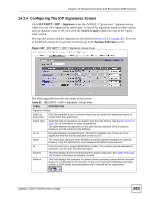
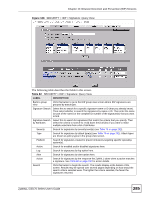
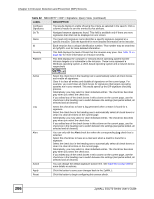
Chapter 14 Intrusion Detection and Prevention (IDP) Screens Table 78 SECURITY > IDP > Signature: Attack Types (continued) TYPE DESCRIPTION Web Attack Web attack signatures refer to attacks on web servers such as IIS (Internet Information Services). SPAM Spam is unsolicited "junk" e-mail sent to large numbers of people to promote products or services. Refer to the anti-spam chapter for more detailed information. Other This category refers to signatures for attacks that do not fall into the previously mentioned categories. 14.3.2 Intrusion Severity Intrusions are assigned a severity level based on the following table. The intrusion severity level then determines the default signature action. Table 79 SECURITY > IDP > Signature: Intrusion Severity SEVERITY DESCRIPTION Severe These are intrusions that try to run arbitrary code or gain system privileges. High These are known serious vulnerabilities or intrusions that are probably not false alarms. Medium These are medium threats, access control intrusions or intrusions that could be false alarms. Low These are mild threats or intrusions that could be false alarms. Very Low These are possible intrusions caused by traffic such as Ping, trace route, ICMP queries etc. 14.3.3 Signature Actions You can enable/disable individual signatures. You can log and/or have an alert sent when traffic meets a signature criteria. You can also change the default action to be taken when a packet or stream matches a signature. The following figure and table describes these actions. Note that in addition to these actions, a log may be generated or an alert sent, if those check boxes are selected and the signature is enabled. Table 80 SECURITY > IDP > Signature: Actions ACTION DESCRIPTION No Action The intrusion is detected but no action is taken. Drop Packet The packet is silently discarded. Drop Session When the firewall is enabled, subsequent TCP/IP packets belonging to the same connection are dropped. Neither sender nor receiver are sent TCP RST packets. If the firewall is not enabled only the packet that matched the signature is dropped. Reset Sender When the firewall is enabled, the TCP/IP connection is silently torn down. Just the sender is sent TCP RST packets. If the firewall is not enabled only the packet that matched the signature is dropped. Reset Receiver When the firewall is enabled, the TCP/IP connection is silently torn down. Just the receiver is sent TCP RST packets. If the firewall is not enabled only the packet that matched the signature is dropped. Reset Both When the firewall is enabled, the TCP/IP connection is silently torn down. Both sender and receiver are sent TCP RST packets. If the firewall is not enabled only the packet that matched the signature is dropped. 282 ZyWALL 5/35/70 Series User's Guide