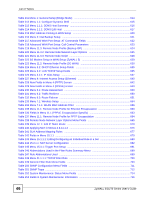
List of Tables
ZyWALL 5/35/70 Series User’s Guide
47
Table 254 System Maintenance Menu Syslog Parameters
.................................................................
718
Table 255 System Maintenance Menu Diagnostic
...............................................................................
724
Table 256 Filename Conventions
........................................................................................................
726
Table 257 General Commands for GUI-based FTP Clients
................................................................
728
Table 258 General Commands for GUI-based TFTP Clients
..............................................................
729
Table 259 Budget Management
...........................................................................................................
741
Table 260 Call History
..........................................................................................................................
741
Table 261 Menu 24.10 System Maintenance: Time and Date Setting
.................................................
743
Table 262 Menu 24.11 – Remote Management Control
......................................................................
746
Table 263 Menu 25: Sample IP Routing Policy Summary
...................................................................
749
Table 264 IP Routing Policy Setup
......................................................................................................
750
Table 265 Menu 25.1: IP Routing Policy Setup
...................................................................................
751
Table 266 Menu 25.1.1: IP Routing Policy Setup
................................................................................
753
Table 267 Schedule Set Setup
............................................................................................................
758
Table 268 Hardware Specifications
.....................................................................................................
769
Table 269 Firmware Specifications
......................................................................................................
770
Table 270 Feature and Performance Specifications
............................................................................
771
Table 271 Compatible ZyXEL WLAN Cards and Security Features
....................................................
772
Table 272 3G Features Supported By Compatible 3G Cards
..............................................................
773
Table 273 3G Features Supported By Additional Compatible 3G Cards
.............................................
773
Table 274 3G Features Supported By Additional Compatible 3G Cards
.............................................
774
Table 275 North American Plug Standards
..........................................................................................
775
Table 276 European Plug Standards
...................................................................................................
775
Table 277 United Kingdom Plug Standards
.........................................................................................
775
Table 278 Australia And New Zealand Plug Standards
.......................................................................
775
Table 279 Japan Plug Standards
.........................................................................................................
775
Table 280 China Plug Standards
.........................................................................................................
776
Table 281 Console/Dial Backup Port Pin Assignments
.......................................................................
776
Table 282 Ethernet Cable Pin Assignments
........................................................................................
777
Table 283 Commonly Used Services
...................................................................................................
783
Table 284 IEEE 802.11g
......................................................................................................................
791
Table 285 Wireless Security Levels
.....................................................................................................
792
Table 286 Comparison of EAP Authentication Types
..........................................................................
795
Table 287 Wireless Security Relational Matrix
....................................................................................
798