HP 6125G HP 6125G & 6125G/XG Blade Switches Security Command Reference - Page 204
root-certificate fingerprint
 |
View all HP 6125G manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 204 highlights
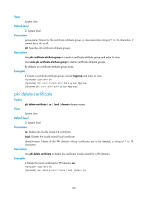
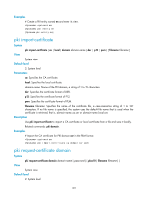
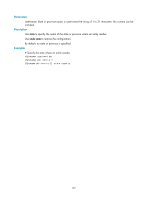
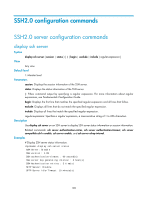
Description Use pki validate-certificate to examine the validity of a certificate. Certificate validity verification examines whether the certificate is signed by the CA and that the certificate has neither expired nor been revoked. Related commands: pki domain. Examples # Verify the validity of the local certificate. system-view [Sysname] pki validate-certificate local domain 1 root-certificate fingerprint Syntax root-certificate fingerprint { md5 | sha1 } string View undo root-certificate fingerprint PKI domain view Default level 2: System level Parameters md5: Uses an MD5 fingerprint. sha1: Uses a SHA1 fingerprint. string: Fingerprint to be used. An MD5 fingerprint must be a string of 32 characters in hexadecimal. A SHA1 fingerprint must be a string of 40 characters in hexadecimal. Description Use root-certificate fingerprint to configure the fingerprint to be used for verifying the validity of the CA root certificate. Use undo root-certificate fingerprint to remove the configuration. By default, no fingerprint is configured for verifying the validity of the CA root certificate. Examples # Configure an MD5 fingerprint for verifying the validity of the CA root certificate. system-view [Sysname] pki domain 1 [Sysname-pki-domain-1] root-certificate fingerprint md5 12EF53FA355CD23E12EF53FA355CD23E # Configure a SHA1 fingerprint for verifying the validity of the CA root certificate. [Sysname-pki-domain-1] root-certificate fingerprint sha1 D1526110AAD7527FB093ED7FC037B0B3CDDDAD93 195