Cisco NME-16ES-1G User Guide - Page 8
x Port-Based Authentication, EtherChannel Configuration Guidelines and Restrictions - p compatibility
 |
UPC - 882658036101
View all Cisco NME-16ES-1G manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 8 highlights
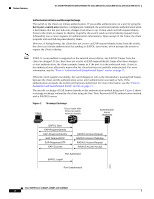
Feature Overview 16- and 36-Port Ethernet Switch Module for Cisco 2600 Series, Cisco 3600 Series, and Cisco 3700 Series Use the option that provides the greatest variety in your configuration. For example, if the traffic on a channel is going only to a single MAC address, using the destination MAC address always chooses the same link in the channel; using source addresses or IP addresses may result in better load balancing. EtherChannel Configuration Guidelines and Restrictions If improperly configured, some EtherChannel interfaces are disabled automatically to avoid network loops and other problems. Follow these guidelines and restrictions to avoid configuration problems: • All Ethernet interfaces on all modules support EtherChannel (maximum of eight interfaces) with no requirement that interfaces be physically contiguous or on the same module. • Configure all interfaces in an EtherChannel to operate at the same speed and duplex mode. • Enable all interfaces in an EtherChannel. If you shut down an interface in an EtherChannel, it is treated as a link failure and its traffic is transferred to one of the remaining interfaces in the EtherChannel. • An EtherChannel will not form if one of the interfaces is a Switched Port Analyzer (SPAN) destination port. For Layer 2 EtherChannels: • Assign all interfaces in the EtherChannel to the same VLAN, or configure them as trunks. An EtherChannel supports the same allowed range of VLANs on all interfaces in a trunking Layer 2 EtherChannel. If the allowed range of VLANs is not the same, the interfaces do not form an EtherChannel. Interfaces with different Spanning Tree Protocol (STP) port path costs can form an EtherChannel as long they are otherwise compatibly configured. Setting different STP port path costs does not, by itself, make interfaces incompatible for the formation of an EtherChannel. After you configure an EtherChannel, configuration that you apply to the port-channel interface affects the EtherChannel. 802.1x Port-Based Authentication This section describes how to configure IEEE 802.1x port-based authentication to prevent unauthorized devices (clients) from gaining access to the network. As LANs extend to hotels, airports, and corporate lobbies, insecure environments could be created. Understanding 802.1x Port-Based Authentication The IEEE 802.1x standard defines a client/server-based access control and authentication protocol that restricts unauthorized devices from connecting to a LAN through publicly accessible ports. The authentication server authenticates each client connected to a switch port before making available any services offered by the switch or the LAN. Until the client is authenticated, 802.1x access control allows only Extensible Authentication Protocol over LAN (EAPOL) traffic through the port to which the client is connected. After authentication is successful, normal traffic can pass through the port. Cisco IOS Release 12.2(2)XT, 12.2(8)T, and 12.2(15)ZJ 8