Netgear GS748Tv5 Software Administration Manual - Page 203
Port Security Configuration
 |
View all Netgear GS748Tv5 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 203 highlights
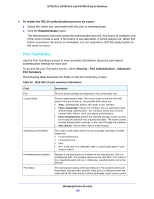
GS716Tv3, GS724Tv4, and GS748Tv5 Smart Switches Port Security Configuration Use the Port Security feature to lock one or more ports on the system. When a port is locked, only packets with an allowable source MAC addresses can be forwarded. All other packets are discarded. To configure the global port security mode: 1. Select Security > Traffic Control > Port Security > Port Security Configuration. 2. In the Port Security Mode field, select the appropriate radio button to enable or disable port security on the switch. 3. Click the Apply button. The Port Security Violation table shows information about violations that occurred on ports that are enabled for port security. The following table describes the fields in the Port Security Violation table. Table 65. Port security violation information Field Port Last Violation MAC VLAN ID Description Identifies the port where a violation occurred. The source MAC address of the last packet that was discarded at a locked port. The VLAN ID corresponding to the Last Violation MAC address. Port Security Interface Configuration A MAC address can be defined as allowable by one of two methods: dynamically or statically. Both methods are used concurrently when a port is locked. Dynamic locking implements a first arrival mechanism for port security. You specify how many addresses can be learned on the locked port. If the limit has not been reached, then a packet with an unknown source MAC address is learned and forwarded normally. When the limit is reached, no more addresses are learned on the port. Any packets with source MAC addresses that were not already learned are discarded. You can effectively disable dynamic locking by setting the number of allowable dynamic entries to zero. Static locking allows you to specify a list of MAC addresses that are allowed on a port. The behavior of packets is the same as for dynamic locking: only packets with an allowable source MAC address can be forwarded. To configure port security settings: 1. Select Security > Traffic Control > Port Security > Interface Configuration. 2. Select the ports or LAGs to configure. For information about how to select and configure one or more ports or LAGs, see Configuring Interface Settings on page 28. Managing Device Security 203