D-Link DGS-3612G Product Manual - Page 401
Login Method Lists, Login Method Lists window, Parameter, Description, Method List Name
 |
UPC - 790069296390
View all D-Link DGS-3612G manuals
Add to My Manuals
Save this manual to your list of manuals |
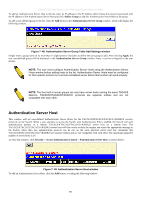
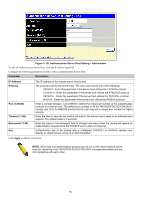
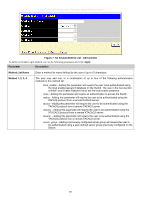
Page 401 highlights
xStack® DGS-3600 Series Layer 3 Managed Gigabit Ethernet Switch Login Method Lists This command will configure a user-defined or default Login Method List of authentication techniques for users logging on to the Switch. The sequence of techniques implemented in this command will affect the authentication result. For example, if a user enters a sequence of techniques, for example TACACS - XTACACS - local, the Switch will send an authentication request to the first TACACS host in the server group. If no response comes from the server host, the Switch will send an authentication request to the second TACACS host in the server group and so on, until the list is exhausted. At that point, the Switch will restart the same sequence with the following protocol listed, XTACACS. If no authentication takes place using the XTACACS list, the local account database set in the Switch is used to authenticate the user. When the local method is used, the privilege level will be dependant on the local account privilege configured on the Switch. Successful login using any of these techniques will give the user a "User" privilege only. To upgrade his or her status to the administrator level, the user must use the Enable Admin window, in which the user must enter a previously configured password, set by the administrator. (See the Enable Admin part of this section for more detailed information concerning the Enable Admin command.) To view this window, click Security > Access Authentication Control > Login Method Lists, as shown below: Figure 7- 51. Login Method Lists window The Switch contains one Method List that is set and cannot be removed, yet can be modified. To delete a Login Method List defined by the user, click the under the Delete heading corresponding to the entry desired to be deleted. To modify a Login Method List, click on its hyperlinked Method List Name. To configure a new Method List, click the Add button. Both actions will result in the same window to configure: Figure 7- 52. Login Method List - Add window To define a Login Method List, set the following parameters and click Apply: Parameter Description Method List Name Enter a method list name defined by the user of up to 15 characters. Method 1, 2, 3, 4 The user may add one, or a combination of up to four of the following authentication methods to this method list: tacacs - Adding this parameter will require the user to be authenticated using the TACACS protocol from a remote TACACS server. 385