Kyocera ECOSYS M6535cidn ECOSYS M6035cidn/M6535cidn Operation Guide - Page 95
Additional Preparations for the Administrator, Sending Documents to a PC, Strengthening the Security
 |
View all Kyocera ECOSYS M6535cidn manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 95 highlights
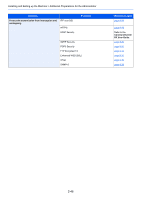
Installing and Setting up the Machine > Additional Preparations for the Administrator Additional Preparations for the Administrator In addition to the information provided in this chapter, the administrator of this machine should check the following, and configure the settings as needed. Sending Documents to a PC To Send to a Shared Folder (Send to Folder (SMB)) To send a document that has been loaded, you need to create a shared folder to receive the document on your computer. Preparation for Sending a Document to a Shared Folder in a PC (page 3-13) To E-mail Scanned Images (Send as E-mail) You can send a scanned original image as an E-mail attachment. E-mail Settings (page 2-53) Strengthening the Security This machine is shipped with two default users registered one with Machine Administrator rights, and another with Administrator rights.Logging in as this user will allow you to configure all settings; therefore, please change the login user name and password. In addition, this machine is equipped with user authentication function, which can be configured to limit the access to this machine to only those who have a registered login name and password. User Authentication and Accounting (User Login, Job Accounting) (page 9-1) I want to... Restrict the users of the machine. Restrict the basic functions that can be used. Prevent another user from handling the documents stored in the machine. Prevent the data stored in the machine from being leaked. Function User Login Auto Panel Reset ID Card Settings*1 Local Authorization Group Authorization Set. Custom Box*2 Data Overwrite*3 Encryption*3 PDF Encryption Functions Completely delete the data on the machine before disposing of the machine. Data Sanitization *1 The optional Card Authentication Kit is required. *2 The optional SSD is required. *3 The optional Data Security Kit is required. Reference page page 9-2 page 8-37 page 9-29 page 9-17 page 9-18 page 5-37 Refer to the Data Security Kit (E) Operation Guide. page 6-30 page 8-36 2-45