McAfee MTP08EMB3RUA Product Guide - Page 148
Overview of scanning process, Types of devices to scan, About active devices
 |
UPC - 731944568133
View all McAfee MTP08EMB3RUA manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 148 highlights
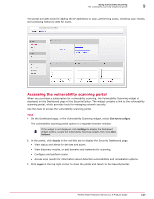
9 Using Vulnerability Scanning Overview of scanning process Overview of scanning process This is the high-level process to configure scans and find vulnerabilities in your network. Each of these procedures is detailed in the sections that follow. 1 Log on to the vulnerability scanning portal. 2 Specify what to scan by one of these methods: • If you know which IP addresses to scan - Add one or more IP addresses. • If you do not know which IP addresses to scan - Add a domain, then run a discovery scan to identify the active IP addresses. IP addresses (and ranges of IP addresses comprising networks) are called devices in the vulnerability scanning portal. 3 Configure the devices you want to scan. This includes selecting the type of device, which determines the standard used for scanning. 4 Configure the devices to accept the McAfee IP addresses where vulnerability scans originate. 5 Create groups where devices can be placed. (Optional) 6 Configure and initiate scans manually, or schedule them to occur at a later time. 7 View results of the scans and suggested remediation tasks (if vulnerabilities were found). Optionally, generate customized reports and schedule remediation tasks. Types of devices to scan Scans target two types of network components. • Device - A single host, IP address, or domain name. • Network - A range of IP addresses. These scan targets are called devices on the vulnerability scanning portal. Before running scans, you must add each device you want to scan to your account on the vulnerability scanning portal. If you are unsure of the IP addresses to add, you can add a domain name and run a discovery scan to identify the IP addresses. To ensure scans that are thorough in scope, we recommend adding your domain name as a device. If you have purchased a single domain license, you are entitled to scan all IP addresses in that domain. To scan multiple IP addresses in separate domains, you must purchase additional licenses. About active devices We recommend scanning all active devices. Active devices are those that are involved in, or connected to networks involved in, collecting, transmitting, processing, or storing sensitive information. Examples of active devices you should scan are: • Filtering devices - These include firewalls or external routers that are used to filter traffic. If using a firewall or router to establish a DMZ (a buffer zone between the outside public Internet and the private network), these devices must be scanned for vulnerabilities. • Web servers - These allow Internet users to view web pages and interact with your websites. Because these servers are fully accessible from the public Internet, scanning for vulnerabilities is critical. 148 McAfee Total Protection Service 5.1.5 Product Guide