Dell PowerEdge M520 Dell PowerConnect M6220/M6348/M8024 Switches Configuration - Page 116
TACACS+ Configuration Example, PowerConnect M6220/M6348/M8024 Switches with TACACS
 |
View all Dell PowerEdge M520 manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 116 highlights
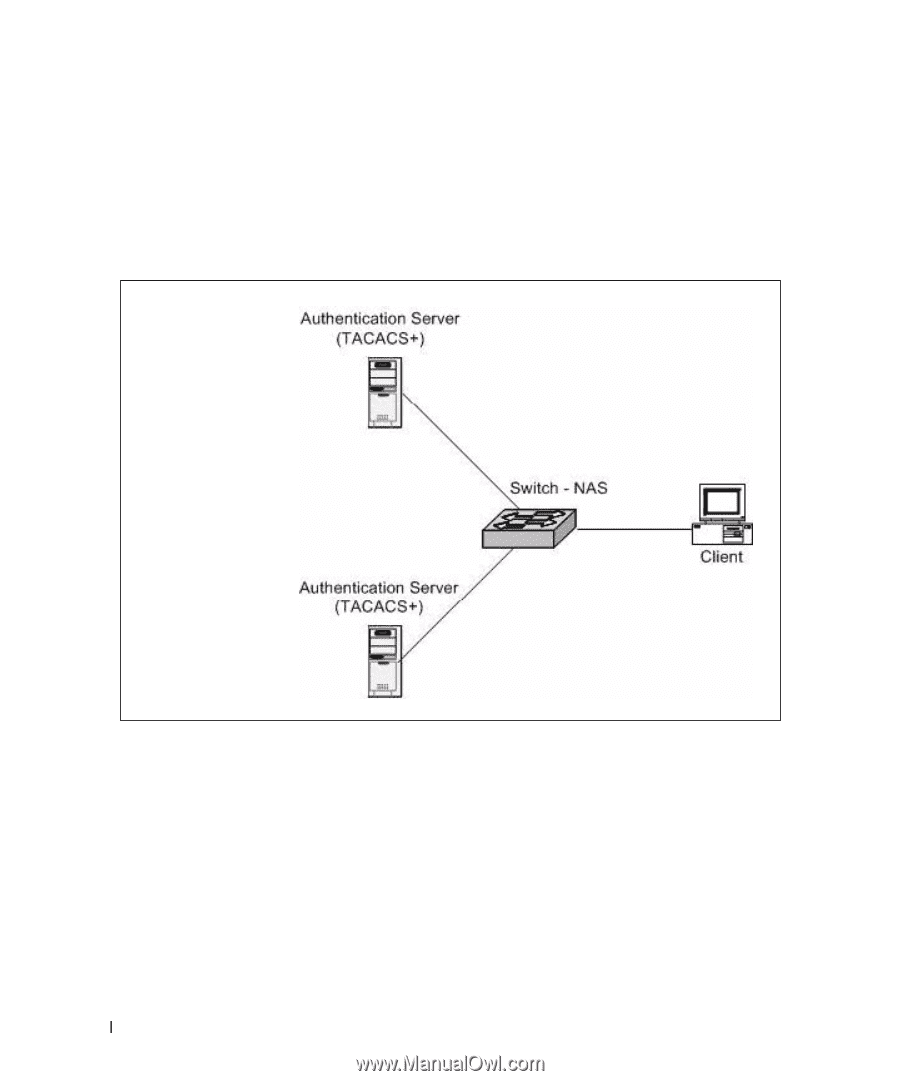
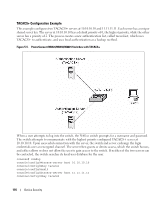
TACACS+ Configuration Example This example configures two TACACS+ servers at 10.10.10.10 and 11.11.11.11. Each server has a unique shared secret key. The server at 10.10.10.10 has a default priority of 0, the highest priority, while the other server has a priority of 2. The process creates a new authentication list, called tacacsList, which uses TACACS+ to authenticate, and uses local authentication as a backup method. Figure 5-5. PowerConnect M6220/M6348/M8024 Switches with TACACS+ When a user attempts to log into the switch, the NAS or switch prompts for a username and password. The switch attempts to communicate with the highest priority configured TACACS+ server at 10.10.10.10. Upon successful connection with the server, the switch and server exchange the login credentials over an encrypted channel. The server then grants or denies access, which the switch honors, and either allows or does not allow the user to gain access to the switch. If neither of the two servers can be contacted, the switch searches its local user database for the user. console# config console(config)#tacacs-server host 10.10.10.10 console(config)#key tacacs1 console(config)#exit console(config)#tacacs-server host 11.11.11.11 console(config)#key tacacs2 116 Device Security