HP A7533A HP StorageWorks Fabric OS 6.1.1 administrator guide (5697-0235, Dece - Page 71
Creating Fabric OS user accounts
 |
UPC - 829160830858
View all HP A7533A manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 71 highlights
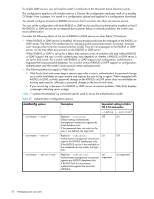
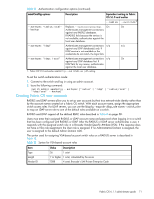
Table 12 Authentication configuration options (continued) aaaConfig options Description Equivalent setting in Fabric OS 5.1.0 and earlier --radius --switchdb1 --authspec "radius;local" Replaces --radiuslocalbackup. On On --backup Authenticates management connections against any RADIUS databases. If RADIUS fails because the service is not available, authenticates against the local user database. --authspec "ldap" Authenticates management connections n/a n/a against any LDAP database(s) only. If LDAP service is not available or the credentials do not match, the login fails. --authspec "ldap; local" Authenticates management connections n/a On against any LDAP database first. If LDAP fails for any reason, authenticates against the local user database. 1. Fabric OS 5.1.0 and earlier aaaConfig --switchdb setting. To set the switch authentication mode: 1. Connect to the switch and log in using an admin account. 2. Issue the following command: switch:admin> aaaConfig --authspec ["radius" | "ldap" | "radius;local" | "ldap;local" --backup] Creating Fabric OS user accounts RADIUS and LDAP servers allow you to set up user accounts by their true network-wide identity rather than by the account names created on a Fabric OS switch. With each account name, assign the appropriate switch access roles. For LDAP servers, you can use the ldapcfg ---maprole to map an LDAP server role to one of the default roles available on a switch. RADIUS and LDAP support all the defined RBAC roles described in Table 8 on page 58. Users must enter their assigned RADIUS or LDAP account name and password when logging in to a switch that has been configured with RADIUS or LDAP. After the RADIUS or LDAP server authenticates a user, it responds with the assigned switch role in a Brocade Vendor-Specific Attribute (VSA). If the response does not have a VSA role assignment, the User role is assigned. If no Administrative Domain is assigned, the user is assigned to the default Admin Domain AD0. The syntax used for assigning VSA-based account switch roles on a RADIUS server is described in Table 13. Table 13 Syntax for VSA-based account roles Item Value Description Type Length Vendor ID 26 1 octet 7 or higher 1 octet, calculated by the server 1588 4 octet, Brocade's SMI Private Enterprise Code Fabric OS 6.1.1 administrator guide 71