McAfee PASCDE-AB-IA Product Guide - Page 64
Table 1: Monitor tab, Table 2: Exclude tab, Click
 |
View all McAfee PASCDE-AB-IA manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 64 highlights
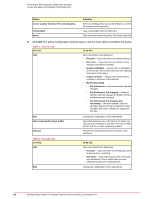
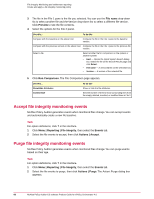
File Integrity Monitoring and entitlement reporting Create and apply a file integrity monitoring policy Option Create a policy based on this existing policy Policy Name Notes Definition Select an existing policy, such as My Default, or another file integrity monitoring policy. Type a meaningful name for the policy Type information about the policy. This field is optional. 6 Click OK. The policy configuration window opens. Use the three tabs to configure the policy. Table 1: Monitor tab Use this: To do this: Add Open the Monitor Item dialog box: • File path - Type a file path to the monitored file(s). • File name - Type a file name to monitor, using wildcard characters as needed. • Include subfolders - Monitor files in subfolders of the file path. This is useful when you use wildcard characters in file names. • Follow symlinks - Monitor files referenced by symlinks or shortcuts in the file path. • Monitoring setting • File Entitlement - Monitors whether a file has changed. • File Entitlement, File Integrity - Monitors whether a file has changed or whether the file's entitlements have changed. • File Entitlement, File Integrity, File Versioning - Monitors whether a file has changed, whether the file's entitlements have changed, and stores changes for supported text files . Edit Max versioned file size (1-4 MB) Remove Change the configuration of the selected file. Select the maximum size of the files in the policy. You can only use versioning on text files. This has no effect on files that do not have versioning enabled. Remove the selected file from the list of files to be monitored. Table 2: Exclude tab Use this: Add Edit To do this: Open the Exclude Item dialog box: • File path - Type a file path to the file(s) you want to exclude from monitoring. • File name - Type a file that you want to exclude from monitoring. This is useful when you use wildcard characters for monitored files. Change the configuration of the selected file. 64 McAfee Policy Auditor 6.0 software Product Guide for ePolicy Orchestrator 4.6