ZyXEL ISG50-PSTN User Guide - Page 267
Bridge Interfaces
 |
View all ZyXEL ISG50-PSTN manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 267 highlights
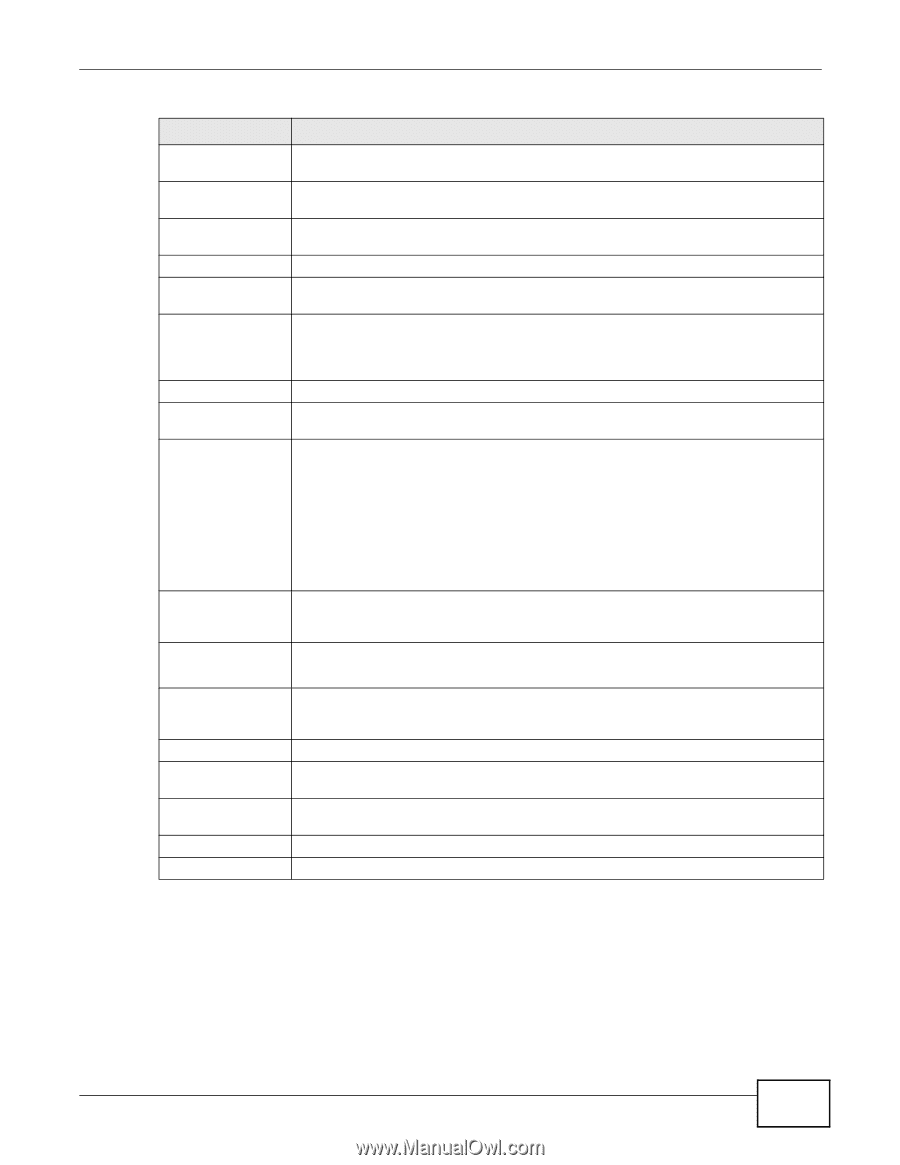
Chapter 12 Interfaces Table 73 Configuration > Network > Interface > VLAN > Edit (continued) LABEL Send Version Receive Version V2-Broadcast OSPF Setting Area Priority Link Cost Passive Interface Authentication DESCRIPTION This field is effective when RIP is enabled. Select the RIP version(s) used for sending RIP packets. Choices are 1, 2, and 1 and 2. This field is effective when RIP is enabled. Select the RIP version(s) used for receiving RIP packets. Choices are 1, 2, and 1 and 2. This field is effective when RIP is enabled. Select this to send RIP-2 packets using subnet broadcasting; otherwise, the ISG50 uses multicasting. See Section 15.3 on page 304 for more information about OSPF. Select the area in which this interface belongs. Select None to disable OSPF in this interface. Enter the priority (between 0 and 255) of this interface when the area is looking for a Designated Router (DR) or Backup Designated Router (BDR). The highest-priority interface identifies the DR, and the second-highest-priority interface identifies the BDR. Set the priority to zero if the interface can not be the DR or BDR. Enter the cost (between 1 and 65,535) to route packets through this interface. Select this to stop forwarding OSPF routing information from the selected interface. As a result, this interface only receives routing information. Select an authentication method, or disable authentication. To exchange OSPF routing information with peer border routers, you must use the same authentication method that they use. Choices are: Same-as-Area - use the default authentication method in the area None - disable authentication Text - authenticate OSPF routing information using a plain-text password Text Authentication Key MD5 Authentication ID MD5 Authentication Key Related Setting Configure WAN TRUNK Configure Policy Route OK Cancel MD5 - authenticate OSPF routing information using MD5 encryption This field is available if the Authentication is Text. Type the password for text authentication. The key can consist of alphanumeric characters and the underscore, and it can be up to eight characters long. This field is available if the Authentication is MD5. Type the ID for MD5 authentication. The ID can be between 1 and 255. This field is available if the Authentication is MD5. Type the password for MD5 authentication. The password can consist of alphanumeric characters and the underscore, and it can be up to 16 characters long. Click WAN TRUNK to go to a screen where you can set this VLAN to be part of a WAN trunk for load balancing. Click Policy Route to go to the screen where you can manually configure a policy route to associate traffic with this VLAN. Click OK to save your changes back to the ISG50. Click Cancel to exit this screen without saving. 12.7 Bridge Interfaces This section introduces bridges and bridge interfaces and then explains the screens for bridge interfaces. ISG50 User's Guide 267