ZyXEL P-202H User Guide - Page 105
Example Firewall Rule
 |
View all ZyXEL P-202H manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 105 highlights
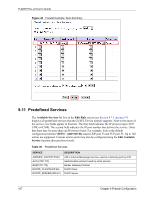
P-202H Plus v2 User's Guide Table 29 Firewall > Logs (continued) LABEL DESCRIPTION EXAMPLE Reason This field states the reason for the log; i.e., was the rule matched, not matched, or was there an attack. The set and rule coordinates ( where X=1,2; Y=00~10) follow with a simple explanation. There are two policy sets; set 1 (X = 1) is for LAN to WAN rules and set 2 (X = 2) for WAN to LAN rules. Y represents the rule in the set. You can configure up to 10 rules in any set (Y = 01 to 10). Rule number 00 is the default rule. not match dest IP This means this packet does not match the destination IP address in set 1, rule 1. Other reasons (instead of dest IP) are src IP, dest port, src port and protocol. This is a log for a DoS attack. attack land, ip spoofing, icmp echo, icmp vulnerability, NetBIOS, smtp illegal command, traceroute, teardrop, or syn flood. Action This field displays whether the packet was blocked (i.e., silently discarded), forwarded or neither (Block, Forward or None). "None" means that no action is dictated by this rule. Block, Forward or None Back Click Back to return to the previous screen. Previous Page/ Click Previous Page or Next Page to view other pages in your log. Next Page Refresh Click Refresh to renew the log screen. Clear Click Clear to clear all the logs. 9.10 Example Firewall Rule The following Internet firewall rule example allows a hypothetical "MyService" connection from the Internet. 1 Click Firewall, then Rule Summary under Internet to Local Network Set. 2 Click a rule number to open the Edit Rule screen. 3 Click Any in the Source Address box and then click SrcDelete. Chapter 9 Firewall Configuration 104