ZyXEL P-202H User Guide - Page 94
Rules Overview, Rule Logic Overview
 |
View all ZyXEL P-202H manuals
Add to My Manuals
Save this manual to your list of manuals |
Page 94 highlights
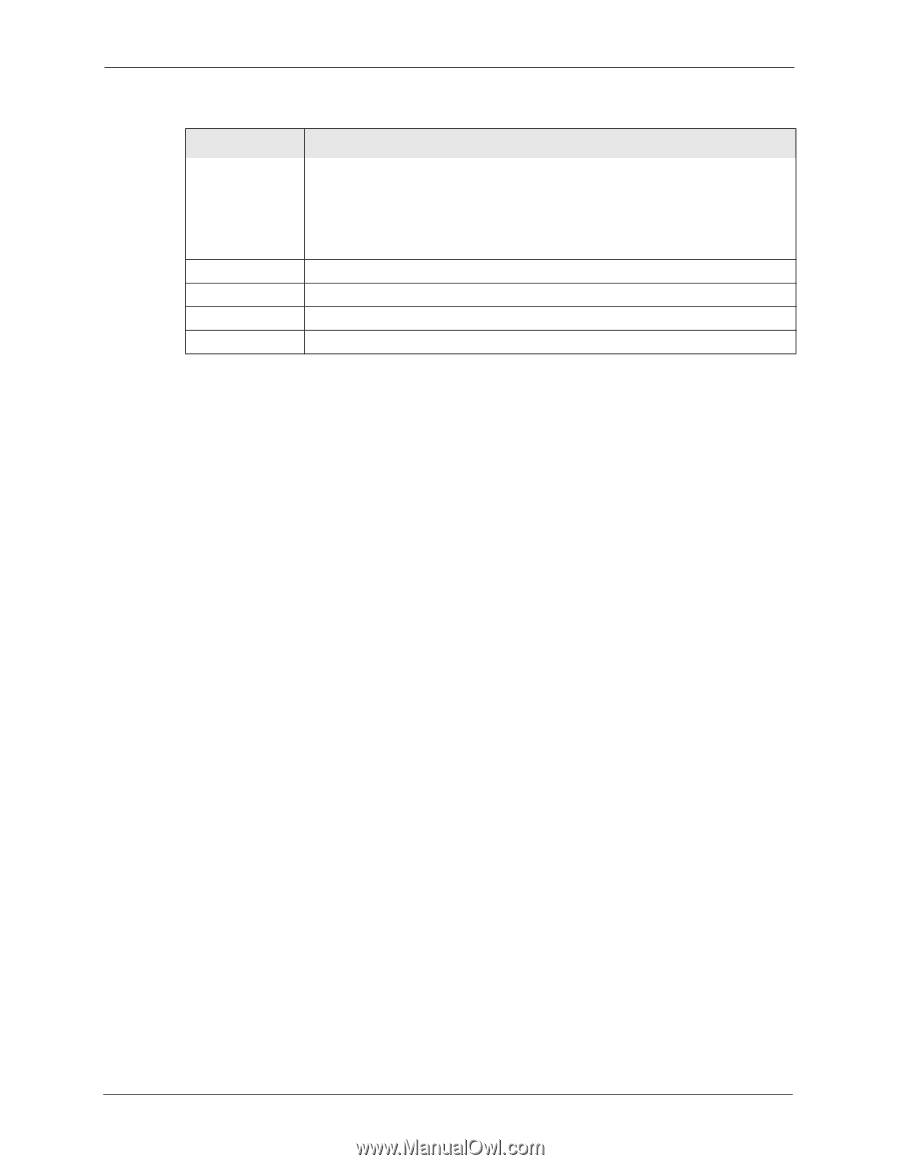
P-202H Plus v2 User's Guide Table 22 Firewall > Alert (continued) LABEL Blocking Time (minute) Back Apply Cancel DESCRIPTION When TCP Maximum Incomplete is reached you can choose if the next session should be allowed or blocked. If you select Blocking Time, any new sessions will be blocked for the length of time you specify in the next field (minute) and all old incomplete sessions will be cleared during this period. If you want strong security, it is better to block the traffic for a short time, as it will give the server some time to digest the loading. Type the length of Blocking Time in minutes (1-256). The default is "0". Click Back to return to the previous screen. Click Apply to save your changes back to the ZyXEL Device. Click Cancel to begin configuring this screen afresh. 9.4 Rules Overview Firewall rules are subdivided into "Local Network" and "Internet". By default, the ZyXEL Device's stateful packet inspection allows all communications to the Internet that originate from the local network, and blocks all traffic to the LAN that originates from the Internet. You may define additional rules and sets or modify existing ones but please exercise extreme caution in doing so. Note: If you configure firewall rules without a good understanding of how they work, you might inadvertently introduce security risks to the firewall and to the protected network. Make sure you test your rules after you configure them. For example, you may create rules to: • Block certain types of traffic, such as IRC (Internet Relay Chat), from the LAN to the Internet. • Allow certain types of traffic, such as Lotus Notes database synchronization, from specific hosts on the Internet to specific hosts on the LAN. • Allow everyone except your competitors to access a Web server. • Restrict use of certain protocols, such as Telnet, to authorized users on the LAN. These custom rules work by comparing the Source IP address, Destination IP address and IP protocol type of network traffic to rules set by the administrator. Your customized rules take precedence and override the ZyXEL Device's default rules. 9.5 Rule Logic Overview Note: Study these points carefully before configuring rules. 93 Chapter 9 Firewall Configuration